The practice of periodic DKIM key rotation strengthens email security and prevents phishing, fraud, and impersonation attacks planned in your business’ name. Leaving your DKIM keys unchanged for a long time could allow attackers to exploit your email-sending domain for attempting malicious activities.
Since DKIM key rotation is critical to your overall email security efforts, it’s important to understand its significance and best practices.
What does DKIM stand for, and what does DKIM do?
DKIM stands for DomainKeys Identified Mail, and is an email authentication method that works on the concept of cryptography. The DKIM signatures within email message headers improve email deliverability and security by filtering out fake emails and processing genuine emails.
To begin implementing, you need to create a pair of public and private DKIM keys for your domain and DKIM record. The public DKIM key is updated to DNS for open access so that recipients’ mailboxes can use it for verification. On the other hand, the private DKIM key is stored secretly on your end.
Now that you know the DKIM meaning and involvement of the keys, let’s move to understanding about a DKIM selector.
What is a DKIM Selector?
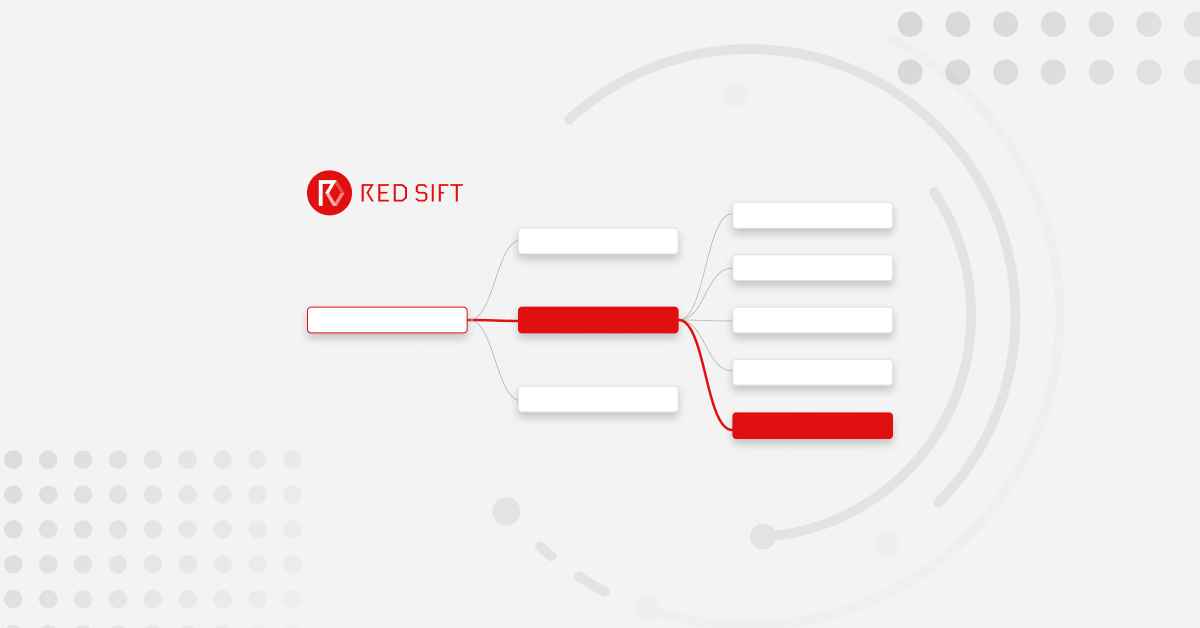
A DKIM selector is a string pointing to a certain public key in your DKIM record. You use an ‘s=’ tag in a signature header field that can be seen in a DKIM email’s technical header.
Recipients’ validators use selectors in combination with the signing domain for locating and retrieving the public key in your DNS.
Why is DKIM Key Rotation Important?
You can rotate DKIM keys by simply replacing the old pair with a new one to authenticate DKIM emails. If a threat actor steals or deciphers your private key, they won’t be able to use them for long if you do regular DKIM key rotation.
Moreover, this practice ensures that signatures are updated, which increases your domain’s email deliverability rate or the ability of your emails to reach the desired recipients’ primary inboxes.
How Often Should DKIM Keys be Rotated?
It’s generally suggested to rotate DKIM keys every 6 to 12 months. However, this isn’t a fixed time period since multiple factors decide the frequency that best suits your domain. Frequent rotation averts hackers from intercepting and decoding your cryptographic keys, but operational limitations can prevent this from happening. While on the other hand, delayed frequency (say, once every couple of years) makes your domain more susceptible to the risk of intercepted or decoded keys.
How Do You Rotate DKIM Keys?
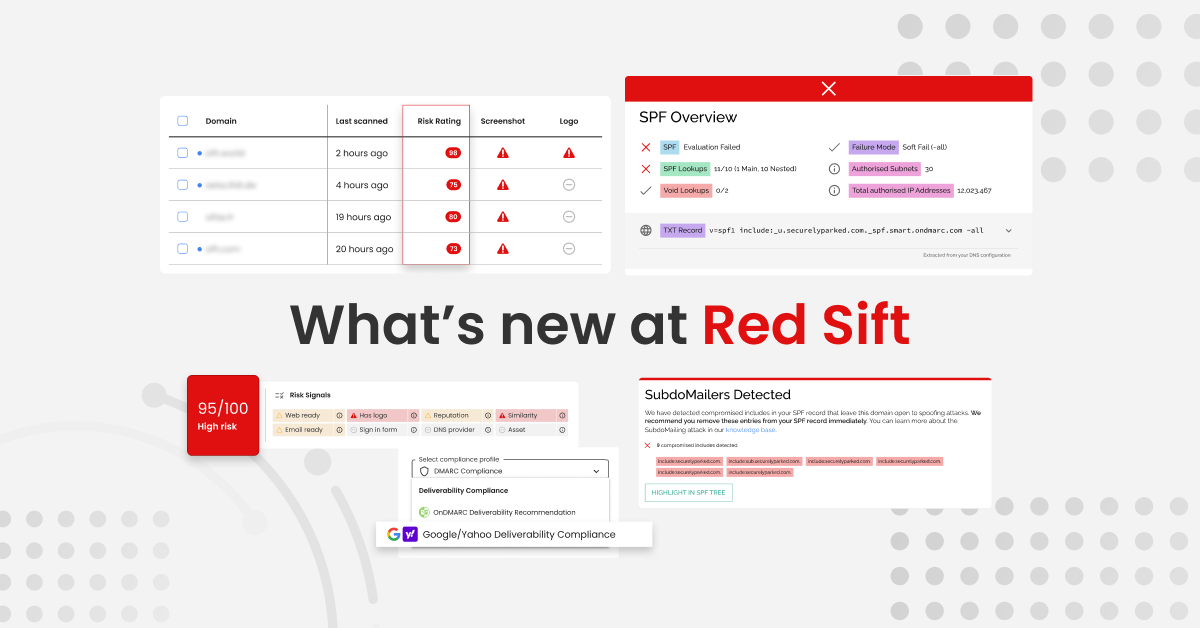
There are a few options to practice DKIM key rotation for enhanced email security. But ensure running your record through a DKIM checker to validate it.
Manual
You can perform manual rotation by making some changes in your DKIM record, note this only applies if you have access to replace the private key:
- Open a DKIM record generator and enter your domain name, followed by mentioning the DKIM selector you want to use.
- You’ll receive the keys to publish on your DNS, replacing the previous record.
- Lastly, share the private key with your email service provider or upload it on your mail server if you manage email transfer on-premise.
Subdomain Delegation
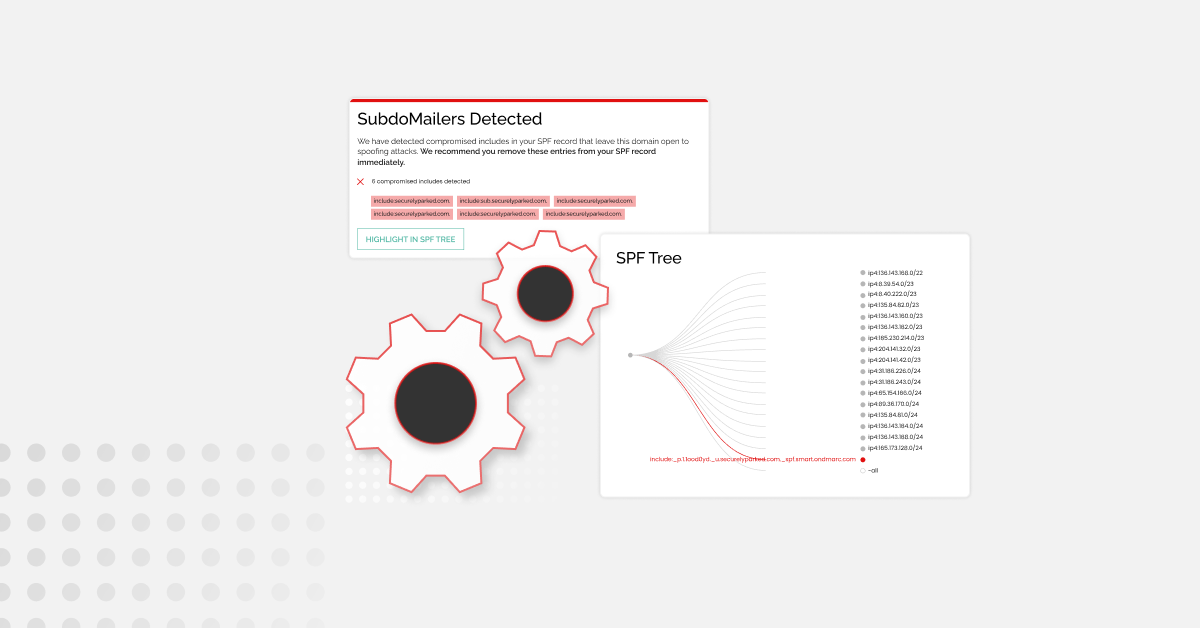
Third-party vendors can periodically rotate DKIM keys for your domain, enabling you to shift your attention to other tasks and get evaded from DKIM management and maintenance responsibilities. Red Sift’s dedicated OnDMARC platform can take charge of all the hassle on your behalf and ensure overall email protection.
CNAME Delegation
CNAME delegation enables domain owners to direct to DKIM record information handled by a third-party vendor. It’s similar to subdomain delegation as you just have to publish some CNAME records on your DNS and the hired third party will handle the key rotation process.
Automatic
Some email vendors and external email service providers offer automatic DKIM key rotation for users. This saves the time spent in zeroing down, troubleshooting, and coordinating remediates for overall DKIM errors.
It’s suggested to rotate DKIM keys using automation over the manual method as the latter is prone to human errors and delays. On the other hand, automatic rotation is faster, effective, and requires minimum involvement of yours.
Best Practices When Rotating DKIM Keys
Following are among the top DKIM key rotation best practices:
- Rotate your DKIM keys periodically; preferably once every 6 months.
- Standardize the DKIM key rotation process for your domain to avoid errors, delays, and redundancies.
- Align key activities like key generation and depreciation for a smooth transition at each rotation period.
- Be prepared for emergency key rotation by pre-publishing the next public key. This is for situations where you detect compromisation of your key pairs.
- Perform regular audits of your DKIM key rotation. As DKIM key rotation best practice, it’s advised to plan audits shortly after a rotation.
How to View and Rotate DKIM Keys in Microsoft Office 365?
To rotate DKIM keys in Office 365, begin by checking if the keys are enabled for rotation. Then follow these steps-
- Sign in to Microsoft 365 Defender portal.
- Go to Email & Collaboration.
- Click Policies & Rules.
- Click on Threat Policies.

Click Email authentication settings

Choose DKIM

- Choose your domain name.
- Slide the toggle from Disabled to Enabled.
- Click on Rotate DKIM keys.

How to Rotate DKIM Keys in Google Workspace?
It’s a bit complicated to rotate DKIM keys in Google Workspace as the domain administrator has to generate a new key, add it to the DNS, and then validate it from the Google admin console. Follow these steps to produce a new DKIM key in Google Workspace:
- Go to your Google Admin Console.
- Go to Menu > Apps > Google Workspace > Gmail.
- Click Authenticate email.
- Choose the domain for which you’ve to generate the new key.
- Click on Generate New Record button.
- From the Select DKIM key bit length drop-down, choose 2048.
- Delete the old keys from the DNS before publishing the new ones.
- Click Generate.
Once you publish the new DKIM key to your DNS, you need to go back to the Authenticate email page in the Google Admin Console, click Start Authentication, and you’re done.
If you’re still skeptical about DKIM practices and management, then head out to our investigate tool to know about errors and ways to fix them.