In late February 2024, ‘SubdoMailing’ became a trending search term overnight. Research by Guardio Labs uncovered a massive-scale phishing campaign that had been going on since at least 2022. At the time of reporting, the campaign had sent 5 million emails a day from more than 8,000 compromised domains and 13,000 subdomains with several reputable brands having fallen victim to this attack.
Over the past few weeks, we’ve been asked what organizations can do to check whether they’ve been impacted by subdomain attacks and how to stay protected. Let’s break it down.
The best tools for checking whether you’ve been impacted by SubdoMailing
Red Sift Investigate
If you’re wondering if you’ve been impacted by SubdoMailing, the best place to start is Red Sift Investigate. All you need to do is send the tool an email and it will dynamically check your email-sending service for any misconfigurations or exposures in real-time.
Red Sift SPF Checker
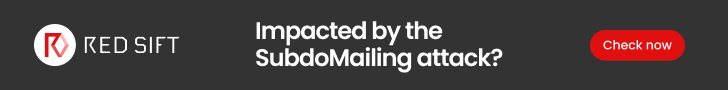
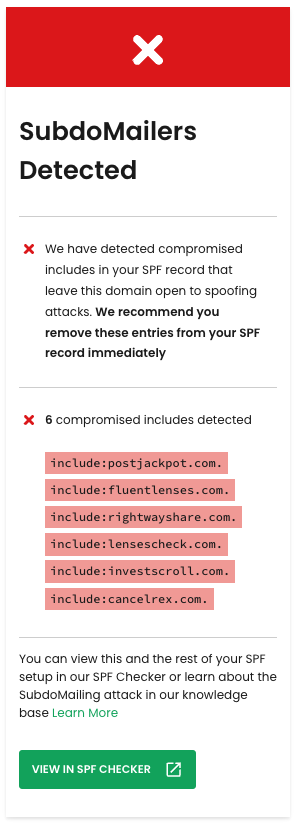
Should Investigate reveal any ‘SubdoMailers’ – also known as poisoned includes – it will prompt you to view them and the rest of your SPF setup in the Red Sift SPF Checker. The SPF Checker allows you to pinpoint any poisoned includes in a dynamic visualization of your ‘SPF tree’, helping to speed up remediation efforts.
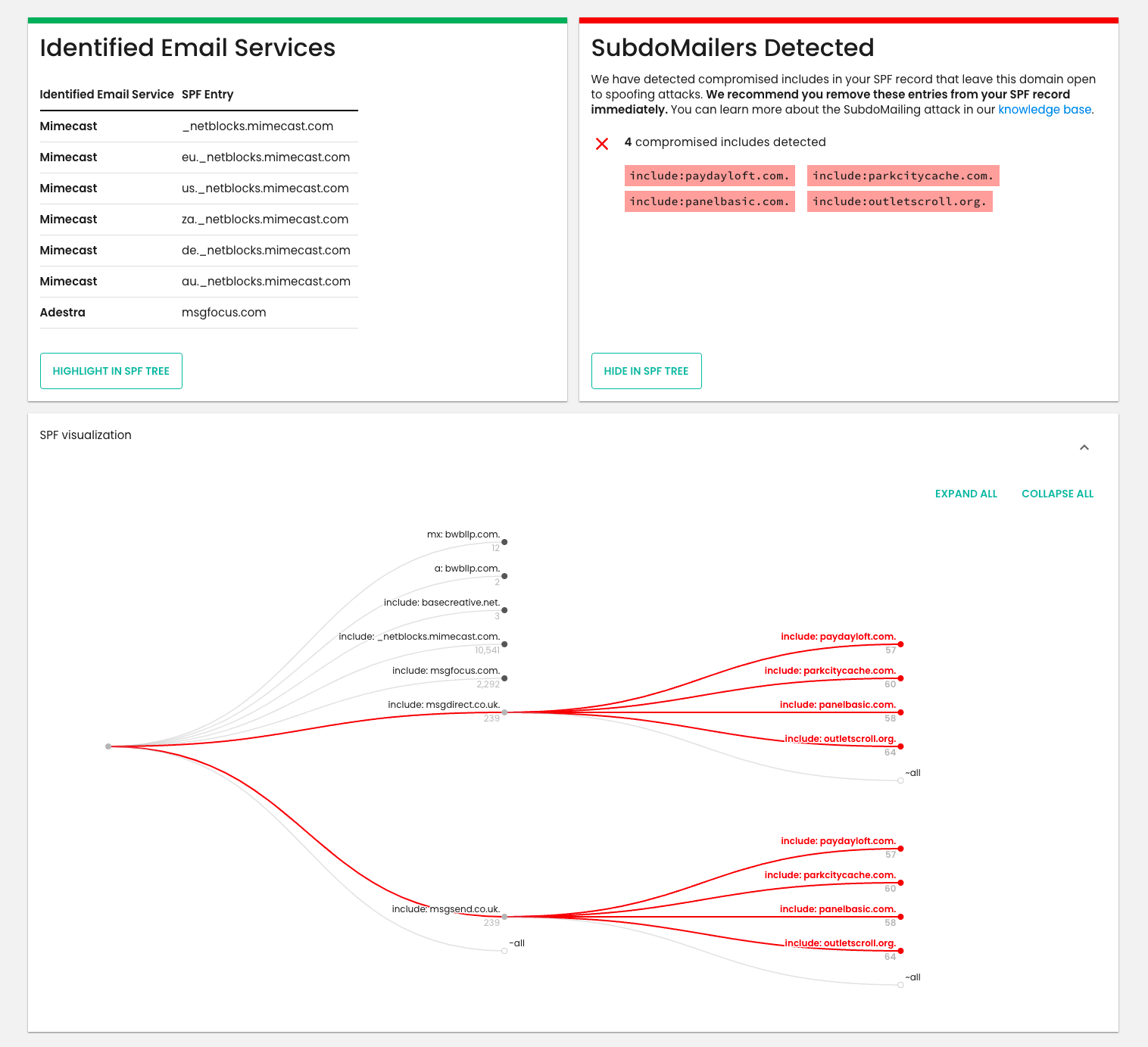
We’ve distilled all of our findings from our ‘known bad list’ so that any domain in the world can be checked to see if their SPF includes are poisoned. We are continuously working on expanding the list – it has grown 500% in one week and we are finding more domains every day.
To learn more about the SubdoMailing campaign and how Red Sift discovered and protected its customers against the attack, read our article.
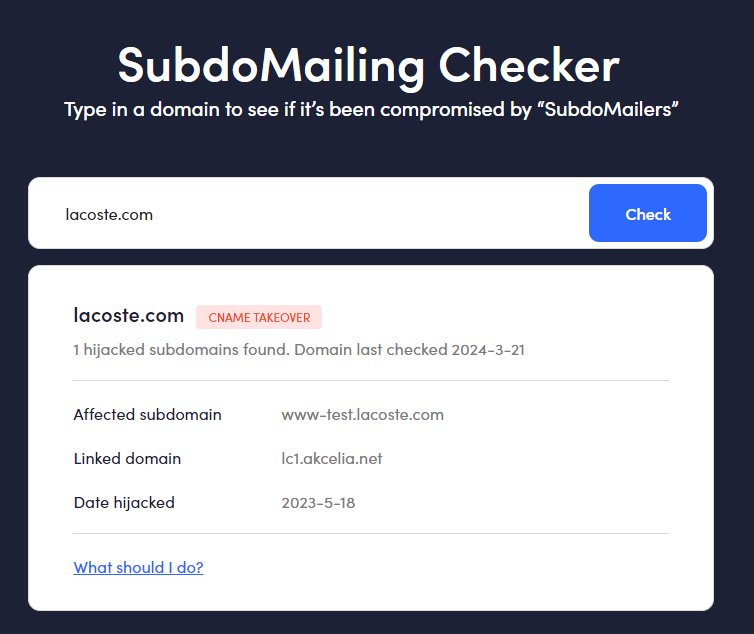
Guardio Labs’ SubdoMailing Checker
Guardio released a SubdoMailing Checker tool that quickly allows users to check if a domain has been compromised. It flags the affected subdomain and the date it was hijacked, along with clear guidance on how to protect your domain in the future.
Static checks for SPF
Many free tools on the internet like MX Toolbox or EasyDMARC’s SPF Tool can look at your DNS records to see if you have a valid SPF record. Since SPF information is publicly available, these tools start with your domain and check if a valid SPF record is published in the DNS. However, these tools won’t tell you whether your SPF setup has been impacted by SubdoMailing. Instead, you would be required to carry out manual checks.
If you have DMARC reporting, you would have to go through your reports and look for suspicious or unknown senders passing SPF. This would indicate that something suspicious is going on.
This is how one of our very experienced Customer Success Engineers discovered an early instance of SubdoMailing in our customer base. He noticed mail was coming from a sender with a poor reputation and a subdomain that appeared unrelated to our customer’s main domain. This subdomain had a CNAME and pointed to an SPF record authorizing services he had never seen. To read the full story of what he uncovered and the next steps that were taken, keep on reading here.
If you don’t have DMARC reporting, you have no visibility into your SPF pass rate, which makes checking for exposures very difficult. To carry out a check, you’d need to analyze each one of your SPF mechanisms and their IPs manually and check various databases to see if they are blocklisted, have bad reputations, or have been used in attacks. In addition, you’d have nothing to compare your current SPF mechanisms against and you wouldn’t know which are active versus which are old or redundant and can be removed.
Both of these methods are time-consuming and complex, especially for organizations that lack IT resources or expertise.
In summary
We highly recommend making use of Red Sift’s Investigate and SPF Checker to get instant insight into any SubdoMailing exposures in your SPF configuration.
If you realize you need more than a free tool as you require implementation and management of email security protocols like SPF, DMARC, and DKIM, check out our award-winning DMARC tool, Red Sift OnDMARC. It offers automated misconfiguration and exposure alerting and makes email security management easy and efficient.
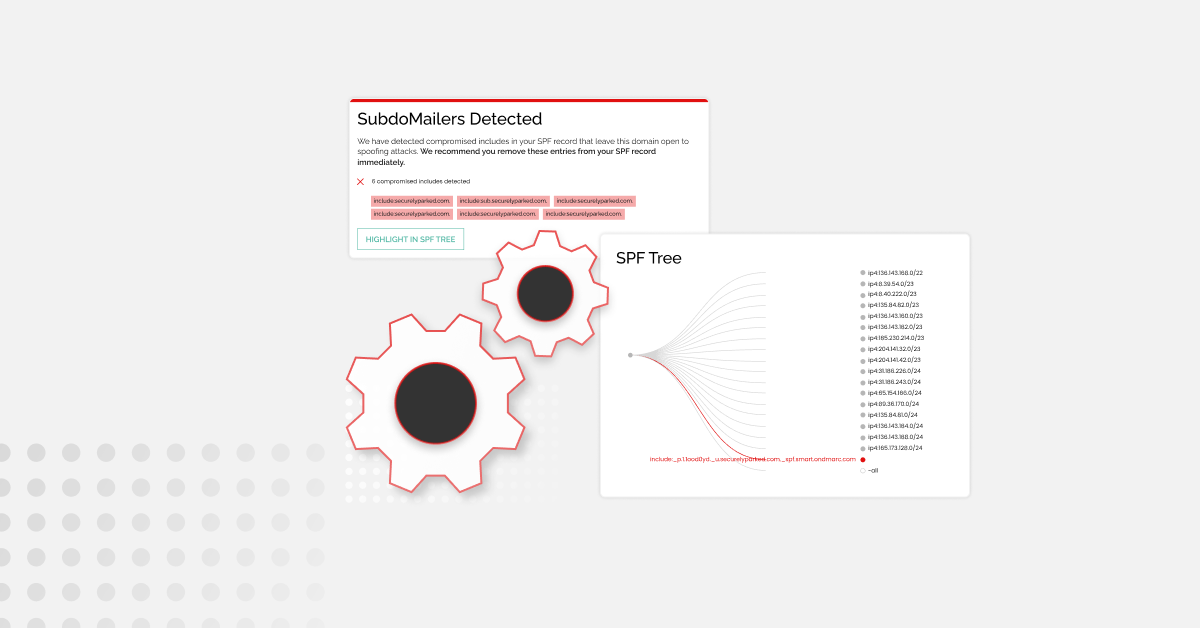
For businesses seeking proactive measures to monitor their domains and subdomains and prevent future attacks like SubdoMailing, consider Red Sift ASM. It conducts vital checks, including domain expiration monitoring to prevent loss of control and identification of dangling records and services for DNS cleanup. Asset discovery and monitoring happen in real-time, providing immediate insights when needed, without delays of days, weeks, or months.