It was recently announced that the EU Digital Operational Resilience Act (DORA) has been passed into law by European Lawmakers. This means that the EU legislation for the financial sector is one step closer to being enforced, and affected businesses need to get ready now.
Below, you’ll find a number of resources designed to help you understand DORA, and how you can begin to improve your organizational resilience to mitigate threats. Also, be sure to keep your eyes open in the coming weeks and months as we continue to roll out more content relating to DORA, and how businesses can prepare.
What is the Digital Operational Resilience Act, and who will it apply to?
The Digital Operational Resilience Act (DORA) is European legislation that requires all financial entities in the European Union (and those that want access to it) to have safeguards in place to manage digital risks. It will apply to the EU financial sector and any business that wants to do business with those in it. It will also apply to third-party software providers. Find out more in our whitepaper.

How to prepare for DORA? 6 Steps you need to take
What do you need to do to prepare for the Digital Operational Resilience Act, and where should you get started? DORA is a lengthy piece of legislation, and while it would be impossible to address every provision that businesses need to prepare for in one eBook, we’ve addressed what our expert believes are the top 6 provisions that are reasonably achievable in a short time frame. Download the eBook to find out more.

Will DORA reduce business disruption, and could Board members face jail if they don’t comply?
The Digital Operational Resilience Act signifies a fundamental shift in how businesses in the financial sector protect themselves and mitigate cyber threats. But what else does DORA mean for organizations and board members? We’ve listed 7 things you need to know about DORA here.

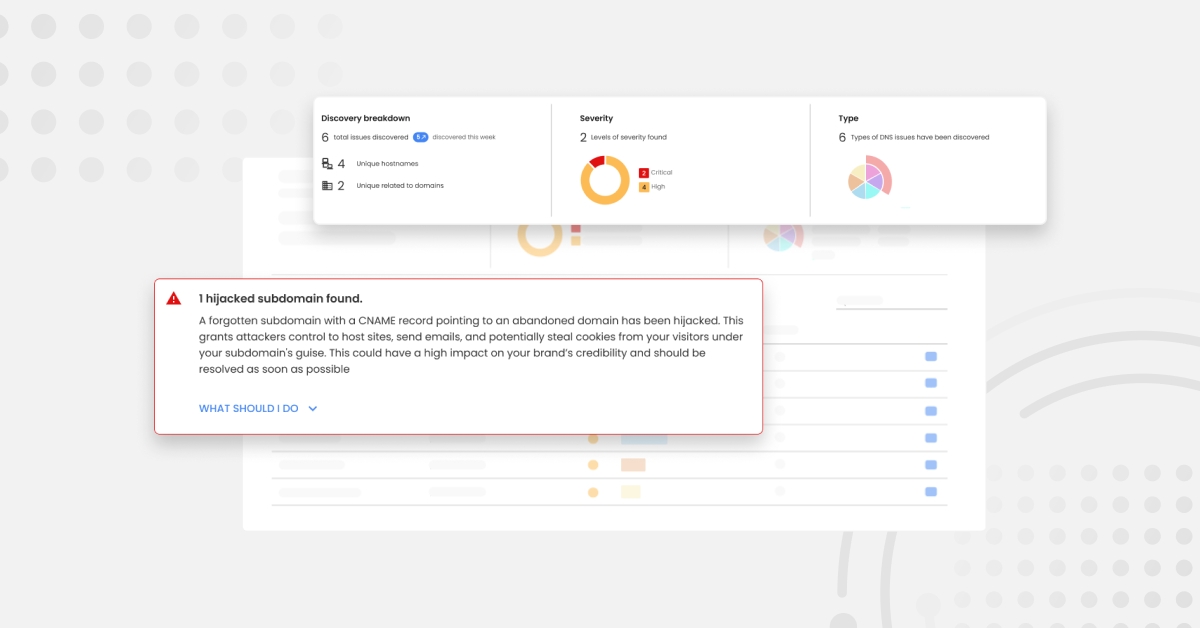
What does email security have to do with digital resilience and DORA?
To comply with DORA, businesses must make provisions in all areas. Email is one of the biggest vulnerabilities in a business’ attack surface, so email and domain security shouldn’t be overlooked in your DORA preparations. Find out more here.

Inherent Risks: from security to resilience
Red Sift Head of Cyber Governance Dr. Rois Ni Thuama discusses how creating value is important, but in today’s world, defending and protecting this value is a necessary part of any business’ resilience strategy. Find out more here.

Value Preservation: Lessons from the Florentine Banker attack
Digital operational resilience and value preservation go hand in hand. In this joint webinar with Checkpoint, Red Sift’s Head of Cyber Governance Dr. Rois Ni Thuama, and Check Point’s Aseel Kayal discuss the fallout from the Florentine Banker attack, and how it could have been avoided. Watch now.

Find out how to prepare for the Digital Operational Resilience Act today
We think that the Digital Operational Resilience Act is long overdue. Businesses deserve clear and comprehensive guidance on how they can mitigate the ever-expanding cyber threat landscape. DORA is here to make lives easier, and businesses better. Plus, it’s not just financial firms and third-party software providers that can benefit, sectors of all shapes and sizes can listen to what DORA says, and use its guidance to make their organizations better, faster, and stronger.
To find out how to mitigate risks relating to email and domain security in preparation for DORA, book your free consultation with Red Sift today.