I recently joined the advisory board of Red Sift.
Why I hear you ask? Outside of the fame and untold riches…
Security is hard. If you have a large team of experts with the appropriate budget it’s hard. And if you’re a small company with limited resources, dreaming of the day you have a large, dedicated security team, it’s extremely hard! Remember, it’s not the size of the organization that defines how valuable a target it is, but the value of the assets to criminals, nation-states, or even unscrupulous competitors.
Similarly, if you’re passionate about helping solve security problems you may want to focus on finding amazing solutions, not building all the ancillary capabilities such as data analytics, logging, visualizations, RBAC, etc.
Red Sift is changing this.
For companies of all sizes, we’re building a scalable, reliable platform hosting security tools and capabilities that solve real problems. Most importantly they are accessible to all, comparatively easy to use, and offer exceptional value.
For developers, we are offering a scalable, reliable, and easy-to-code-for platform that takes care of all the ‘non-core’ parts of the solution, plus access to advanced capabilities such as data analytics and machine learning.
I’m hugely passionate about ‘democratizing security’ and enabling businesses to secure their systems and data with the best possible solutions. The vision the Red Sift founders have aligns extremely closely with these beliefs.
Our aim is nothing short of revolutionary;
- Companies will have access to advanced capabilities at realistic price points
- Developers will have
access to an advanced platform providing an array of critical features ‘out of the box’
By linking these two ends of the same equation we hope to create a thriving community developing amazing security tools that really meet the needs of organisations.
Given these synergies between the Red Sift vision and my belief in how important it is to make security available to all I’m excited to be onboard, and really looking forward to contributing to the vision and direction.
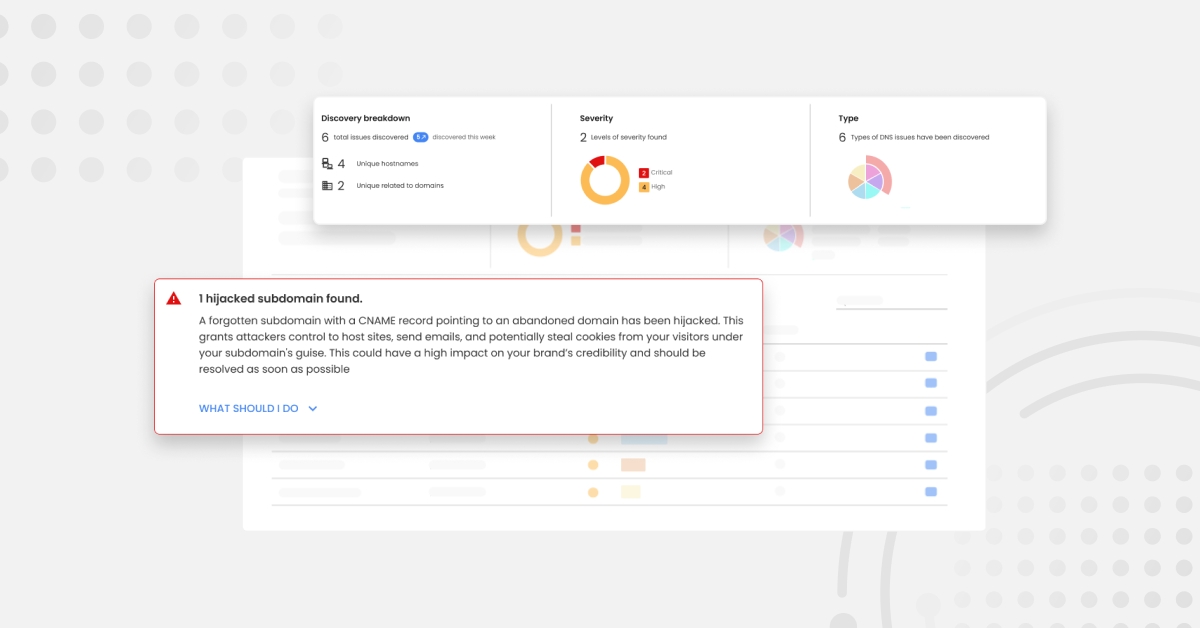
With my background working in technology and security roles across companies ranging in size from 25 people to General Electric, I hope to bring some real guidance around what organisations are looking for and the problems we are all trying to solve. Examples of this include the need for simplifying security and providing just what is required vs. a bloated feature set. The excellent OnDMARC, OnINBOX and OnDOMAIN already follow this principle.
This focus on simply meeting key requirements will help ensure that the Red Sift proposition will become the go-to platform for organizations’ technical security needs.
I’m also close to a few security startups, and am pretty confident a platform such as this would have greatly aided them during the bootstrapping process!
As the platform grows, the ability to easily aggregate the view across the different apps an organization uses will enable a one-stop view of an organization’s current security posture.
Hop on board as we build this new security community!
Find out more about Red Sift people, platform, and products at redsift.com.