With the upcoming release of our advanced threat protection software OnINBOX, we’ve put together a fun game for you to play at home called Find the Phish.
Find the Phish is our phishing simulation game where you have to spot which email is the phishing email. But be warned – it’s not as easy as you might think!
How to play Find the Phish
We give you a choice of 2 emails and you have 30 seconds to decide which one is the phish. Giving you no help would be pretty horrible of us, we get that, so we’ve included a handy feature to toggle OnINBOX on or off as you need.

Our advanced threat protection software OnINBOX makes it easy to spot a phish because it tells users how to ACT.
What is ACT?
A = authenticate
We authenticate the email by evaluating the security protocols the sender has in place. The stronger their security, the lower the risk of you being spoofed by a familiar partner, supplier or other contact in your supply chain.
C = content
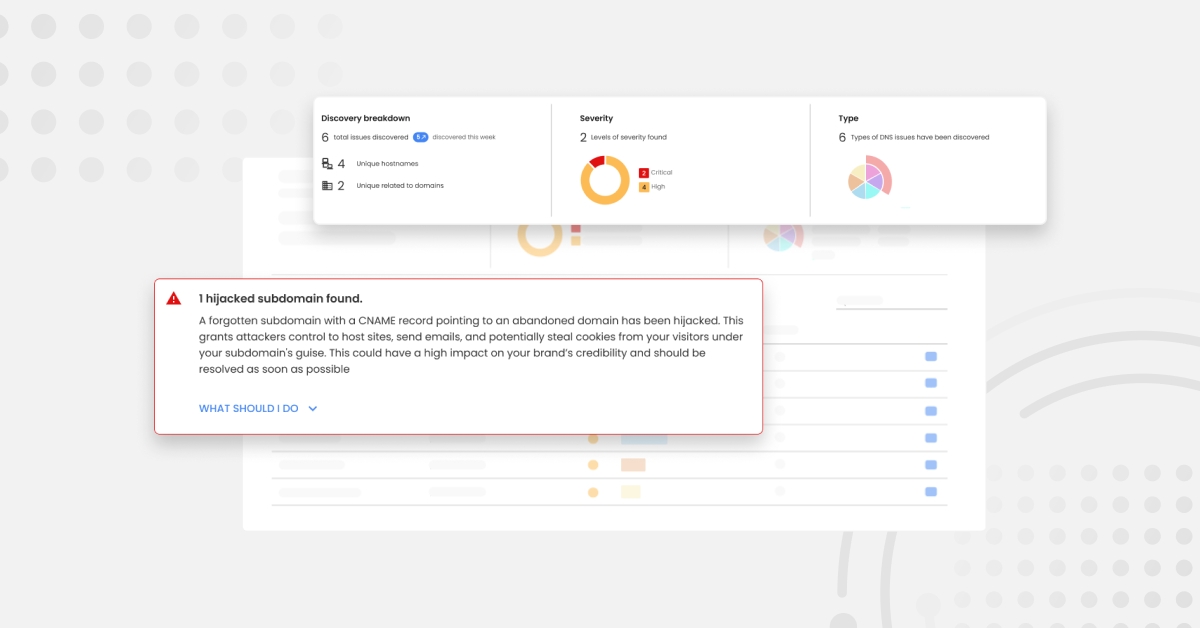
We scan the content of your emails to highlight hidden signals that might cause you harm, like malicious URLs or a hijacked domain. This is combined with advanced machine learning models that empower OnINBOX to spot non-technical threats with social-intelligence by analyzing human language and behaviour. This means your employees don’t have to!
T = trust
OnINBOX learns about the way you interact with people to identify threats and build up your very own trust network. It takes one click to classify a contact with confidence based on the results OnINBOX gives you.
If any one of A, C or T fails, the letter turns red and you know not to trust anything inside the email you’ve received – it could be a phish!
We hope you enjoy the game and be sure to share it with your friends and work colleagues! You can find out more about OnINBOX below.