Red Sift, the cognitive data platform that provides cloud-based email security solutions, has launched its inaugural partner program and purpose-built portal in the midst of global economic uncertainty and increased pressures on the channel to continue delivering best-in-class solutions.
The new program has been designed to support new and existing partners during these unprecedented, work-from-home times – simplifying how partners can supply customers with essential cybersecurity defences without having to engage in complicated hardware installations.
Red Sift’s portfolio of cloud-based security solutions includes:
- OnDMARC
- Mandated by both the Cabinet Office (2016) and Department for Homeland Security (2018), organizations are now required to configure the DMARC email protocol to prevent domain impersonation
- The average sales cycle for OnDMARC is 30 days, ensuring a quick turnaround. High margins are a given with further discounts for deal registrations
- OnINBOX
- Implemented alongside OnDMARC, users can close the loop on the phishing problem
- OnINBOX’s technical risk assessments have recently been updated with the Covid-19 NLP Model – enhanced social-intelligence to alert users to social engineering attacks.
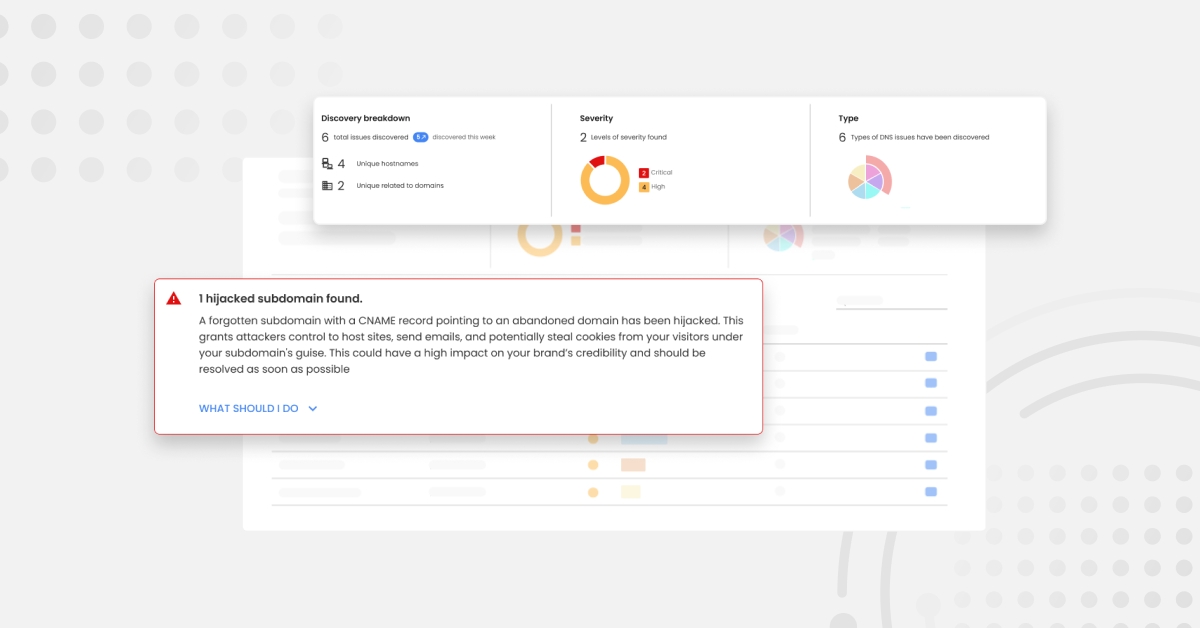
- OnDOMAIN
- OnDOMAIN rapidly uncovers and takes down impersonation domains.
- Upload your brand assets to OnDOMAIN’s logo library and it will train itself to recognize them across the web. This helps identify unauthorized use of your organization’s assets.

“Whether you’re a VAR, systems integrator or MSP, you have a number of obligations to work towards throughout each year and our aim with this program is to make sure that partnering with us is a productive and profitable relationship without complication,” said Neil Crossley, Channel Director at Red Sift. “This is really about rewarding focus, rather than size – partners come in many shapes and sizes, but it’s about engagement, transparency and a true partnership – those that demonstrate focus and loyalty are given the right kind of prioritisation and rewards.”
“Red Sift’s partner program delivers everything we need – it empowers partners to take Red Sift’s portfolio to market, confident that enablement and support are integral to the vendor-partner relationship,” said Joseph Hedegaard-Ganly, Information Security Specialist at Saepio. “The clear and generous structure of the program reinforces our faith in Red Sift as a key partner for Saepio. It was clear from the off that Red Sift’s partner portal had been built from scratch, with the efficacy and simplicity for partners to easily manage collaboration. Simple and effective tracking of combined efforts, with seamless communication and collaboration tools make this the best portal we’ve seen”.
“Opportunistic scammers are utilizing this global pandemic that has given rise to so many employees navigating the uncharted territory of remote working,” continued Crossley. “Phishing scams come in all manner of guises, from urgent security alerts to fake invoices, and too many organizations, regardless of size, still don’t have adequate defences in place. There is a significant opportunity for partners to take on our 360° email protection suite with its low cost of ownership and high yields, while enabling them to add value to their customers.”