Cybercriminals have always exploited human weakness to successfully execute cyber attacks. Ask any vendor what the weakest link in the chain was 15 years ago and they’d offer the human up for sacrifice. Fast forward to 2022 and the answer is likely to be the same. So why, when cybercrime techniques continue to become more sophisticated, is the industry still relying on education as the key to organizational defence?
Many organizations rely on cybersecurity training
Most companies hold cybersecurity training (and even primary schools are teaching four and five-year-olds how to stay safe online) as an essential part of the HR induction. This has been the case for over a decade, with 95% of information security professionals stating they train end users to identify and avoid phishing attacks.
In fact, of the organisations who evaluate the risk that individual end users pose to overall security postures, 3 out of 4 rely on security training awareness performance to gauge that risk.
To teach or not to teach
So, for many businesses today, it’s about teaching to be aware of potential threats and therefore not fall victim to a phishing attack. But can anti-phishing be taught, and if so, should it be?
Education and awareness do have a role to play in any cybersecurity strategy. But with the inherent vulnerabilities in the human element of security, education should be considered as a measure that fortifies, rather than replaces, technology-powered cybersecurity solutions. Employees should form a supportive line of defence within a strategy that positions technology at the helm.
Too cool for school
Companies who rely on education and awareness alone put themselves and their employees at greater risk of attack and under greater time and resource strain.
An education-based approach is complex to maintain. It needs to be a part of the onboarding process, but it also needs to be repeated at regular intervals, while taking into account employee turnover, leave, and competing business priorities. More often than not, it applies a one-size-fits-all approach to education, rather than accounting for those employees who may be more receptive to classroom-based learning versus those who respond to participatory learning such as online courses or attack simulation.
Education-based approaches often lean towards blaming rather than empowering employees, by putting the responsibility of spotting clever phishing emails onto staff when it could be more effectively and efficiently shouldered by an automated technology solution – don’t make employees your human firewall.
That’ll teach you
In contrast, an anti-phishing solution underpinned by technology doesn’t rely on regular reinforcement, excessive resources, or accountability for accountability’s sake. Of course, it does require some technical understanding and resources to implement correctly. But its main benefits are its reliability, automation, and efficiency.
A technology-based solution is built to spot vulnerabilities quickly and accurately, analyze and report efficiently, and can even be leveraged to educate and build awareness with employees as it protects. A good solution should be data-driven, adaptable, and available to all organizations.
The key to building an effective cybersecurity defense among employees is to arm users with the tools necessary to effectively defend against attacks.
With an endpoint threat protection solution, greater visibility over the network’s threat landscape, and a strong employee education program, businesses can best mitigate against the threat of phishing, the vector used to launch 91% of today’s cyber attacks.
How can Red Sift help?
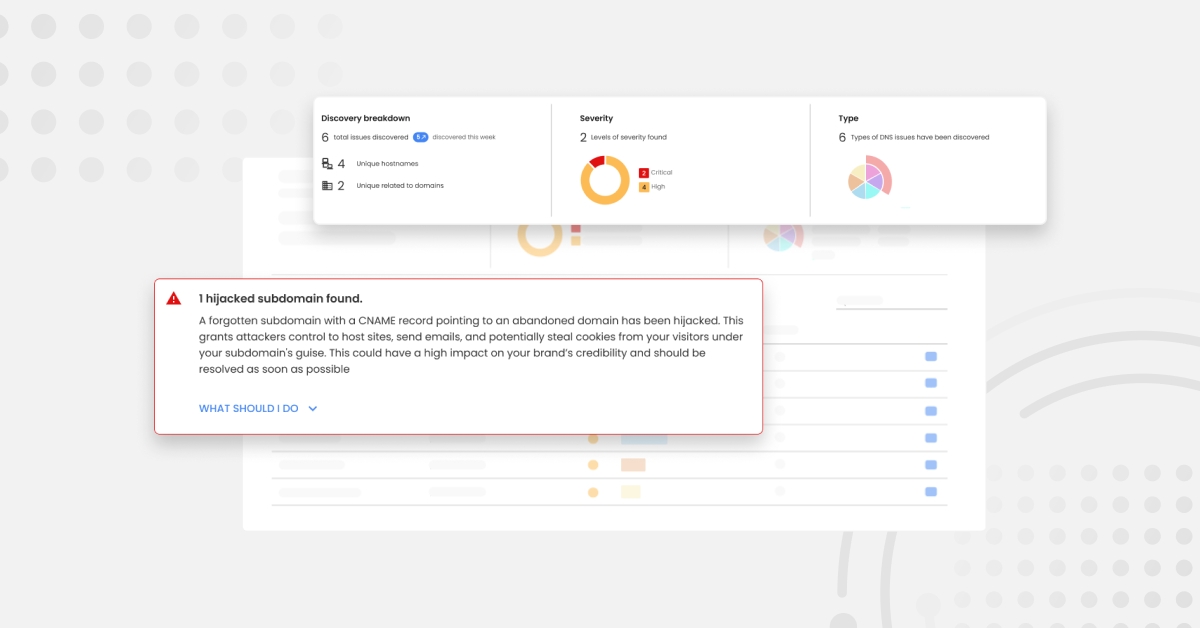
The Red Sift data analysis platform is purpose-built for the challenges of cybersecurity. Products on the Red Sift platform include OnDMARC, OnINBOX, and OnDOMAIN, SaaS applications that work together to close the net on the phishing problem by blocking outbound phishing attacks, analyzing the security of inbound communications, and providing domain impersonation defense.
To find out how our technology-based approach can help your organization mitigate the threat of phishing, book your Red Sift platform demo today.