Let’s talk about impersonation in the cloud-era.
It is very easy to impersonate a domain that is not protected by DMARC. Please refer to part 1 of this blog series if you’re unaware or unsure of what DMARC does.
How is my domain being impersonated?
There are many spoofing methods, all of which are simple to access and simple to use as a cybercriminal.
Cloud hosting companies like AWS and Google Cloud, other high reputation cloud-based senders like Sendgrid, or even public websites, can be used to impersonate an unprotected domain. Cybercriminals can easily spin up a server to send emails on behalf of a vulnerable domain, or simply use a cloud platform to send out malicious emails.
Let’s take Sendgrid as an example. Sendgrid is a cloud platform for marketing and transactional marketing email. Like many high reputation cloud senders they have good controls in place to prevent abuse of their systems and play well with modern standards for making the internet, and email specifically, a better place. However, when it comes to impersonating someone on email with targeted intent the last mile of protection is up to the domain owner.
Let’s walk through this with 2 examples.
Scenario 1:
A company called SofasDeliveredToYou uses Sendgrid to send legitimate emails to their customers. SofasDeliveredToYou has Sendgrid in the SPF record for sofasdeliveredtoyou.com (ie they are whitelisting this sending source to send on their behalf) but SofasDeliveredToYou has no DMARC in place.
Can Sendgrid be used to impersonate sofasdeliveredtoyou.com?
Yes
Does the email get through because Sendgrid is in SofasDeliveredToYou’s SPF record?
No, Sendgrid being in their SPF record has nothing to do with the ability to spoof the sofasdeliveredtoyou.com domain.
Why?
The SPF check is done on the Return-Path/Mail-From address of the email. Sendgrid by default uses an address that points to sendgrid.net. This means that the receiving server of the email will check for an SPF record at sendgrid.net and this SPF check will pass because Sendgrid authorizes their own servers to send emails and therefore this spoof email will be delivered.
Okay… so you’re saying that anyone can use Sendgrid or a similar cloud service to impersonate my unprotected domain successfully
Yes, critically there is no control in the SPF or SMTP standard that prevents this sort of email from being sent. User facing email clients may choose to highlight this situation e.g. Gsuite on the web interface will indicate that this email was sent ‘via sendgrid.net’ but this means little to end users. This is where DMARC comes in. with DMARC protection (p=reject mode) on the “From” address, the receiving server will also check if the domain used during the SPF check is the same as the domain used in the “From” address. If the domains are different, DMARC alignment will fail and the email will not be delivered. This is why it is so important to get DMARC configured correctly.
Scenario 2:
In this scenario we have a legitimate organization called Wish Wing in a DMARC policy of reject and a spoofer in a DMARC policy of reject, both with Sendgrid configured in the SPF record.
The spoofer tries to impersonate Wish Wing’s domain wishwing.com. They use the Wish Wing’s “From”.
Will this email get through?
No, this email will be blocked.
How does this work?
Given wishwing.com has DMARC in compliance mode, Sendgrid will only be able to send an email from wishwing.com when the Wish Wing account attempts to send it. Impersonation attempts will be completely blocked.
But the spoofer was using Sendgrid too. Where does the control come in?
Wish Wing have first of all verified that they own the domain with the Sendgrid service. They then have configured Sendgrid on their end in their SPF record as well as with DKIM. They will have resolved the return path to point to their own domain in the process of deploying DMARC. They are in a DMARC policy of reject.
Wish Wing added include:sendgrid.net to their SPF record as an authorized sending service. Additionally, they have published one or more DKIM public keys in their DNS using either TXT or CNAME records. Once this has been carried out, Wish Wing’s emails will pass both SPF and DKIM and will also align for DMARC. This means the domains used for SPF and DKIM will match the “From” domain that they are using to send emails.
The spoofer is unable to verify that they own the domain wishwing.com and therefore cannot send emails that align in terms of SPF and DKIM. DMARC will then fail and the emails will be blocked from reaching the intended recipient’s inbox.
Will Sendgrid allow you to send from a return-path that you don’t own?
No, they will only allow you to customize the Return-Path header once you have verified you own the “From” domain or are a user in that domain.
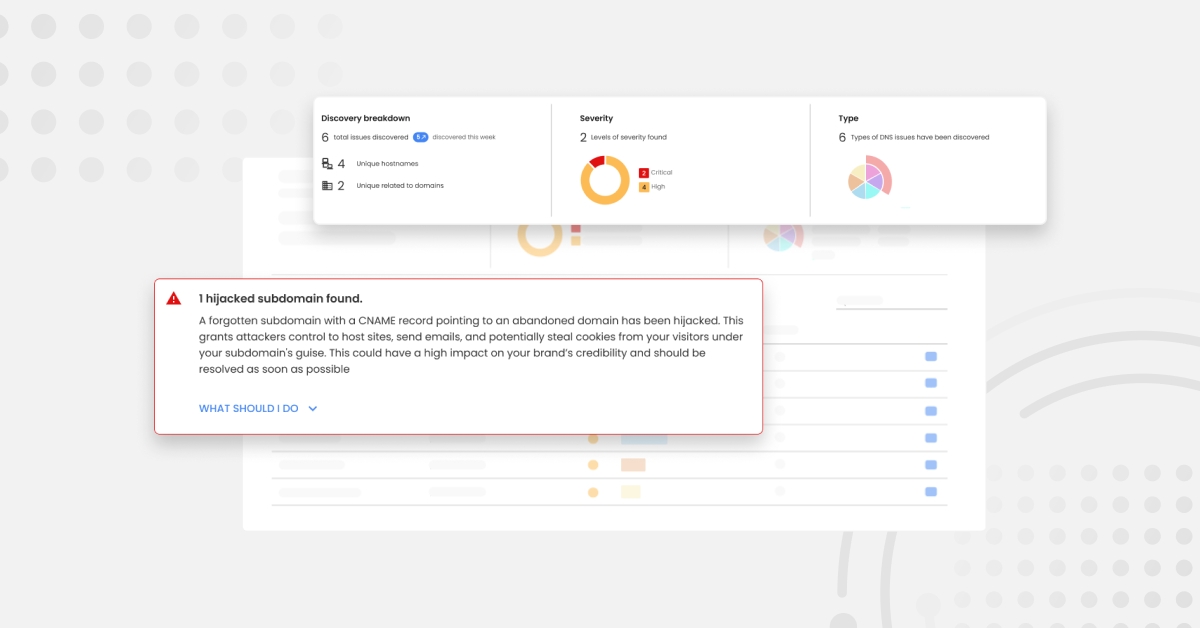
What about cloud vendors that do not have this control in place?
If a cloud vendor does not have the security or controls in place to verify the sending domain, and customize the Return-Path header, anyone will be able to use their service to spoof unprotected domains. Even if the sending domain is protected and in DMARC policy of reject, emails will still go through as the spoofer can achieve From address and Return-Path alignment which is what is required for DMARC to pass. An alignment means that there is a match between the domain used in the From address and the domain used in the Return-Path header.
For example: From address is user@alignment.com and Return-Path header is mail@alignment.com. In this case, both domains after the @ symbol are the same so there is an alignment and DMARC passes. Subdomains of each other are also allowed, the domains do not have to be an exact match.
Dedicated IP?
Using one or multiple dedicated IPs further enhances your overall security posture as those IPs will only be associated with your domain. You will no longer be sharing the same IP reputation with others, as with using a shared pool of IP addresses but in exchange, the reputation of these IPs is entirely up to you and your organisation needs to follow best practices to ensure you don’t blacklist yourself.
Having DMARC protection in conjunction with a dedicated IP address will provide you with further peace of mind as your domain will be fully protected from spoofing and your IP / domain reputation will not be ruined by bad senders using the same pool of IPs. Depending on your plan with Sendgrid, you may have dedicated IP included.
For support with deploying DMARC and helping you to get to p=reject status whereby any email that fails DMARC validation (ie fraudulent email) will be blocked from reaching the recipient’s inbox, try out our 14-day free trial.
A blog co-written by Ivan Kovachev, Customer Success Technical Lead at Red Sift, and Emma Horsfield, previously Head of Sales Enablement at Red Sift.