A strong brand takes time and effort to cultivate.
It’s certainly worth the effort, strong branding can be integral to the success of a business. In fact, 46% of consumers will pay more for brands they trust. It’s no wonder that brand protection is creeping up the priority lists of global businesses.
Traditionally, brand protection has been the responsibility of legal and brand professionals. However, brand abuse is becoming more complex and brand abusers are becoming more tech-savvy. That’s why several departments should now be taking a vested interest in brand protection.
Marketing
Marketers are responsible for building and shaping a company’s brand over time. On average it takes 5-10 years for bigger corporations to build up and establish a successful brand.
However, if that brand is not protected, all that work building trust can be undone in minutes.
So, marketers should take a keen interest in monitoring how a brand is being protected. That way, they can be confident that brand abuse will not undermine their efforts.
Legal
A company’s legal team will want to ensure that brand infringement, fraud, and abuse are prevented.
A common form of brand abuse is lookalike websites misusing an organization’s assets. It is the responsibility of a legal team to ensure that their brand’s names and logos are registered as trademarks. This allows such lookalike websites to be challenged and taken down.
85% of brands say they experienced trademark infringement in 2019. Three-quarters of these trademark infringements led to litigation.
Security Operations & Information Security
Many cyberattacks start with brand impersonation, fake websites, and other forms of online brand abuse. So, security operations and information security professionals need to be poised to prevent this.
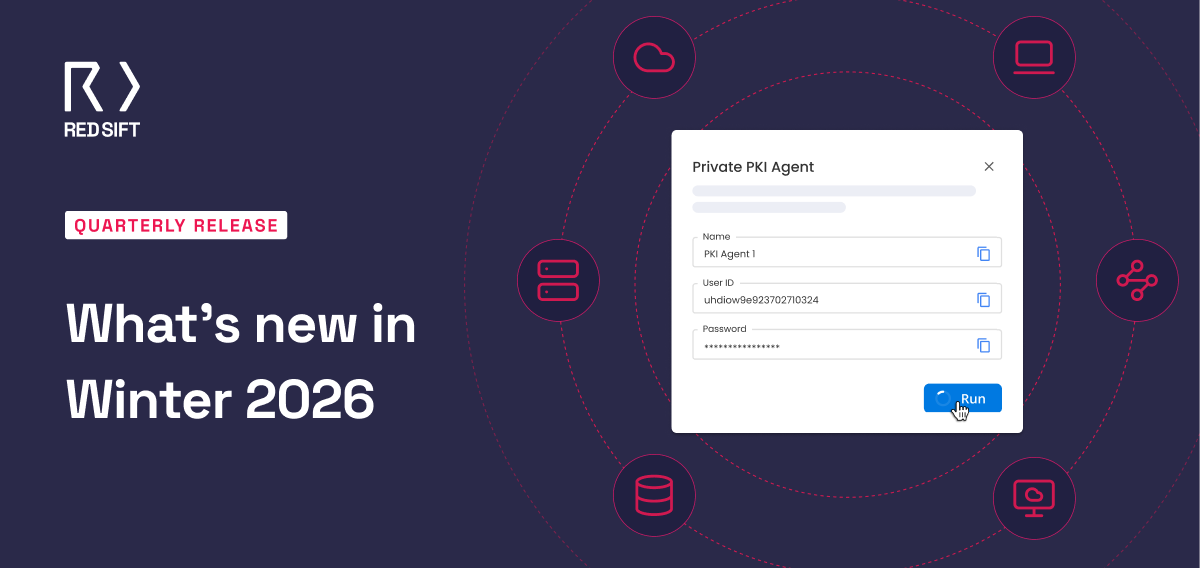
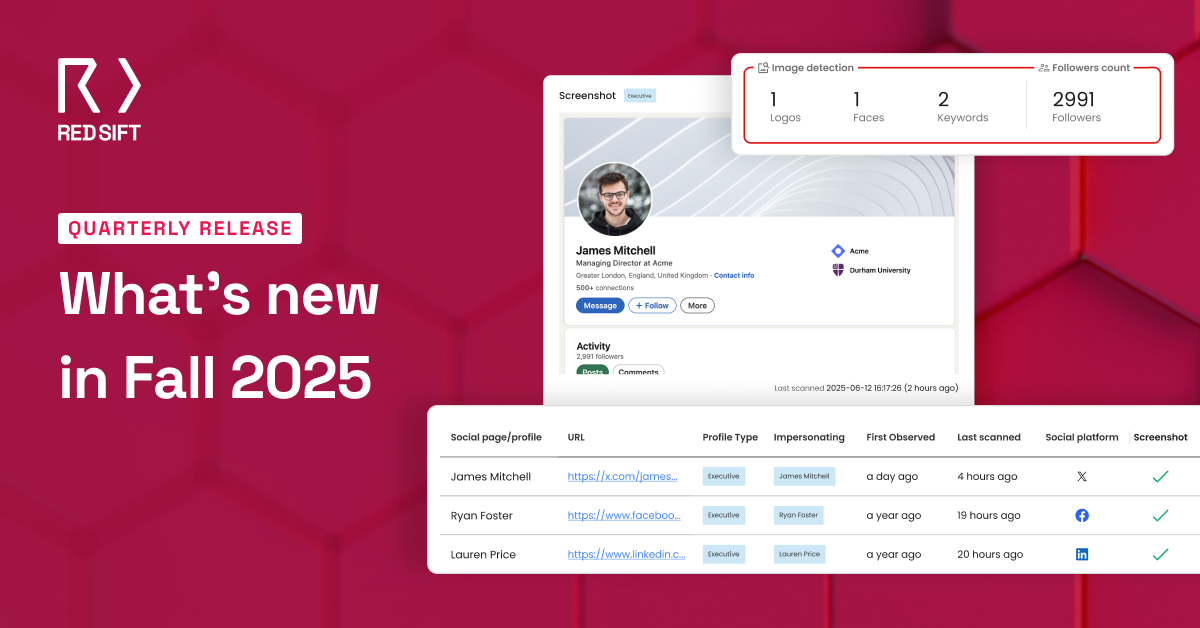
Specialized software allows aspects of online brand protection to be automated. For example, services like Brand Trust can monitor millions of newly registered hostnames to find impersonation domains. They can also scan for unauthorized uses of an organization’s logo and other assets. IT teams should ensure that such tools are employed as part of an organization’s brand protection strategy.
Additionally, suffering a data breach is a surefire way to damage your brand’s reputation and lose the trust of your customers. As a result, ensuring that customer data is secure should be a key priority for IT teams.
And… Everyone else?
While many people feel that brand protection is not in their domain, it is, in fact, their problem.
71% of UK consumers say they’ll stop purchasing from a company altogether if their trust is broken. Conversely, brands that win trust are rewarded with more sales, advocacy, and long-term retention.
It’s clear then that trust in a brand can make or break an organization’s success. So, every department should be a little bit invested in their organization’s brand protection.
To find out more about how our platform can contribute to your organization’s brand protection strategy, download our eBook today.