
It gives me great pleasure to announce that we have accepted $2 million in seed capital led by White Star Capital and Oxford Capital. We are excited to have such a well respected group of investors who believe in the team and our vision along for the ride.
When I first started the process, I took some time to talk to a few founders in my network who had recently been involved in early stage fundraising. While this isn’t my first venture, I wanted to get a sense of what raising a seed from institutional investors in 2016 was like. I gained some great insight but one answer I was unable to pin down was the amount of time and energy a process like this takes. Startups are by their nature small ventures and taking leadership out for a fundraising process takes a material % of the capacity of the organization out of play and is an incredibly distracting exercise. I have seen it stall a business before and was keen to understand the timing and impact around the process in today’s climate so that we could plan appropriately. Hard data here wasn’t easy to come by, individual founders knew it was all consuming and it typically ‘took some time’ but the metrics were subjective. Now every process is unique but a few firm data points can help establish a baseline. Traditionally, any sort of metric across an organic process like a fundraise is pretty hard to get at so there is little information out there. I decided to dog food our own platform and make a Sift for it.
Everyday data sources such as email, messaging platforms, web applications and IoT devices generate vast amounts of data, most of which lacks structure and is difficult to aggregate and summarise. Because of this, it often remains archived without us being able to draw any valuable insight from it. Red Sift allows our users to easily interconnect these disparate sources and join data between them to receive insights or automate workflows. We do this through the use of “Sifts” — smart, open source micro services that run computations on your data securely to deliver information in your dashboard or messaging channels. Sifts can be created by us or the community as our platform allows developers and eventually regular users to create their own Sifts simply and rapidly.
Given that there was little data I could use to predict, I wanted to capture the analytics for the future and keep track of the process through the eyes of our platform. Here is what I created to help me track my time expenditure.

Most processes these days leave a trail in your Inbox. Buying a house, organising a major event, finding a job, executing a due diligence; whatever it might be, you are likely using your email account to progress the task and it leaves a trail in your Inbox. Specialist tools exist for the narrowest of market verticals but they don’t apply to mess that is most processes. Red Sift provides first class support for an Inbox as a data source and can embed analytics inside Gmail. It can turn that stack of messages into something that intelligence can be computed upon and insight gathered without having to move or export the data anywhere else. In addition, as it is fully integrated, it will react in real time to updates — no data entry required. All I needed to do was classify the messages I wanted measured. I dropped a label on them and made my Sift select only those communications.
At a high level, I wanted to understand the impact the process was having on our time so we could track, adapt and use the signal to figure out what was working and what we needed to change. Note that I created this representation in the style of the excellent web comic xkcd by Randall Munroe as I am a huge fan and his stuff makes me laugh. As most founders would agree, anything that makes you smile during a fundraise is a win.
Let’s look at each of the metrics I coded up in turn.
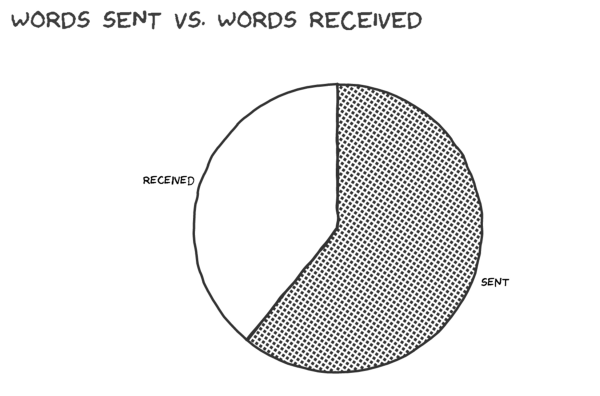
Our strategy was fairly traditional, we made our outreach via warm introductions to ensure we had the best shot at an open door. The data seems to hold up, I didn’t waste much time with firing shots into the dark. Most communication related to this process produced a response and the volume of time spent drafting email was balanced.

We are all familiar with the sprawl of cc lists that build around business communication. Thankfully, VCs in our sample set do not have that problem to a significant degree. Individuals on a thread are mostly relevant when they are copied in as they tend to respond and engage at some point.
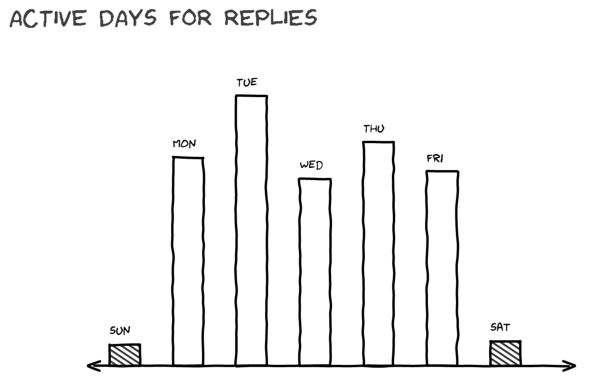
One interesting behaviour we noticed early was the feeling that Monday was a quieter day than we expected. Looks like Tuesday was a measurably higher traffic day for our prospects. I typically tried to block out Mondays to work on the product given that we saw this pattern emerge early.

The grand summary table breaks it all down. A bit over 3 full days at the keyboard spent reading and writing email spread over 33 weeks and a funnel that started at the top with ~53 prospects to get to our final outcome. My Sift has used a heuristic to estimate the time spend reading and responding to communication though it’s obviously inexact in the current form. While there is an error margin, in the future we can use these analytics to establish a baseline and help us plan future activities.
For the purposes of brevity and in the interests of anonymity, I have kept the details fairly high level. There is a lot more signal in my Inbox and calendar covering phone calls / pitches / coffees and my Sift can dig a lot deeper such as correlating time-to-reply with final outcome and estimating response times. Developers and the curious can look under the hood. You can fork and modify them to suit your own purposes and run them live on your own data.
Rahul Powar, Founder & CEO
Humor-Sans used under the SIL Open Font License, Version 1.1






