Let’s get one thing clear from the start; we’re not accusing you of deliberately abetting criminals, but anyone with a sloppy cyber and email security setup is most likely unwittingly aiding them. Now we’re pretty sure you’ll have seen the below quote somewhere before, but today we’re hijacking it to prompt some thoughts about essential cybersecurity.
“The only thing necessary for the triumph of evil is for good men to do nothing”
Edmund Burke, Irish statesman, economist, and philosopher
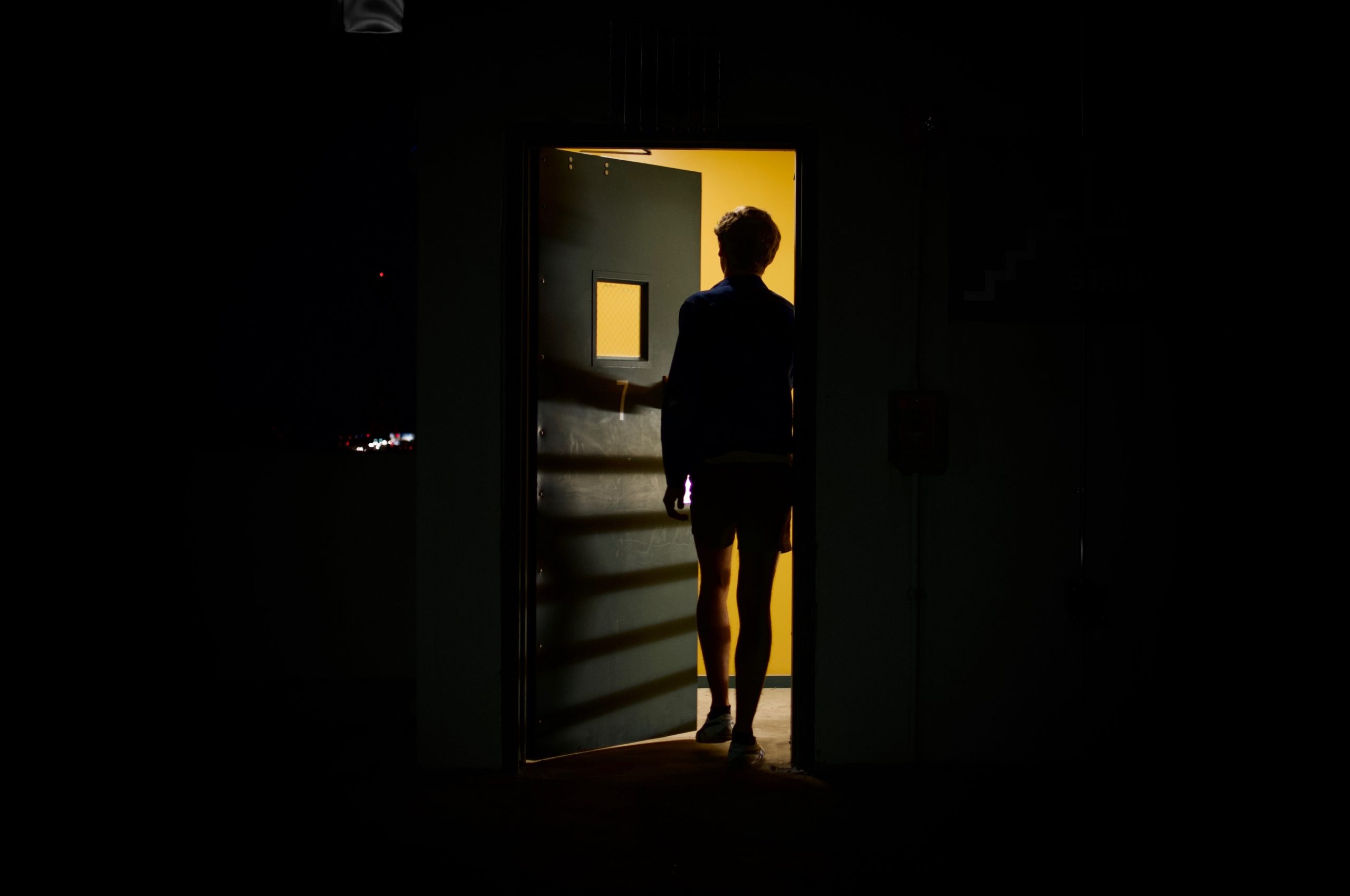
The modern cybercriminal isn’t a mysterious hooded hacker
Consider for one moment the modern cyber-criminal. Not the mysterious hooded hacker that seems to be in every stock photo, you know, this guy:

We’re talking about the “adequate pernicious toerags” that Dr Ian Levy of the NCSC warned against. These guys (and girls!) know that the easy money isn’t to be made by hacking their way past the multiple (expensive) defences of high street banks, or by the well-known Nigerian Prince spam emails. For that perfect balance of effort vs reward, we can safely that in 2021, targeted phishing email scams are now the cybercriminal’s weapon of choice.
The success of these campaigns isn’t just in how cleverly the criminals craft their messages, or who they choose to target, but in the vast quantity of unprotected companies which are at their disposal to mimic.
To fall victim to impersonation, a company doesn’t need to be in the FTSE100 or be a social media star, it just needs to be one that the intended target has a trusted relationship with.
2021 cybercriminals exploit existing reputations
This could be a solicitor the target is using to buy a house, their local hairdresser, their favorite clothing brand, or long-time car insurer. Whichever business the scammer chooses to impersonate, they ultimately rely on the established trust already there to fool the recipient into sending them money, personal information, or opening dodgy attachments.
And these cybercriminals aren’t just after your customers’ money and data. They could well impersonate your domain in a Business Email Compromise (BEC) attack, pretending to be the CEO or Head of Accounts for your company, and trick unsuspecting employees into handing over your data, credentials, paying invoices, and more.
So other than making sure you’re not a victim, how can you help?
The first thing to do is make sure your company domain is protected from exact impersonation (email spoofing) is by fully-implementing DMARC at a policy of p=reject. DMARC (Domain-Based Message Authentication, Reporting, and Conformance) is the only way to stop cybercriminals from stealing your email identity and using it to carry out such scams. Without this essential layer of email authentication, your company brand is available to fraudsters – globally – to use to give their fake emails that vital air of authenticity, and make them much harder to spot.
It’s easy enough to check if you do have DMARC , just type your email into our domain checker and we’ll let you know straight away. Then you can either relax, safe in the knowledge no one is taking your name in vain, or you can get the ball rolling at your company with a conversation with your CISO about how DMARC will protect employees and customers from phishing attacks that use your email identity.