In the world of cyber and email security, terms can soon become entrenched, and any newcomers can easily be left bewildered by the barrage of new terms to know. So, we’ve compiled a short, jargon-busting, no-nonsense overview of what these email security terms mean that will take you from beginner to boffin.
What is Email Spoofing?
Email Spoofing (or Exact Domain Impersonation) is when an email is created from a fraudulent sender address via exact domain impersonation. It might look like a real email, but that’s because it’s been cleverly designed for you to think so – it arrived in your inbox because the spoofer is using a legitimate email domain without authorization. Most of us have received emails from spoofed domains at some point — banks, councils, or HMRC are some of the most common.
What is Phishing?
Phishing is when an attacker sends an email out to trick the recipient into sharing personal details or clicking on a link. Basic phishing emails are sent out en masse with no specific targets. They bait recipients with offers of money or reward, or they use scaremongering, e.g. a bank account compromise, in a bid to get them clicking a hyperlink or sharing sensitive info.
What is Spear Phishing?
Spear phishing is targeted phishing. The emails target specific, known individuals — employees or customers — in an organization. Spear phishing emails most often mimic emails from within the target organization or a closely linked partner organization, so recipients are more likely to think the sender is legitimate.
What is Whaling?
Like the name suggests, it’s when scammers go for the big guns: a person of professional status like a CEO or senior executive who has access to cash or company secrets. A whaling email will be cleverly crafted to convince a specific recipient to open a link or download a program, for example by duping them into thinking they’ve received a real court summons or serious legal complaint. The email can appear to come from an internal source, not just external, at which point it may also be given the similarly jargonistic term ‘CEO fraud’.
What is Business Email Compromise (BEC)?
Business Email Compromise (BEC) is an umbrella term used to describe phishing attacks that target an organization
by impersonating its domain. The attacker relies heavily on Social Engineering, and crafts a phishing email designed to look like one from someone inside the business (usually the CEO). The main aim of this type of attack is to steal money or sensitive data. Examples of BEC attacks include Ransomware, CEO Fraud, and Vendor Fraud.
What is Typosquatting?
More dramatically known as ‘URL hijacking’, typosquatting is when an attacker owns a fake site purporting to be from a known brand and uses it for malicious purposes. Typosquatters are there waiting for you when you accidentally type Gpple.com or Facenook.com. They convince you that their website is legitimate by making it look like the real deal, then when you enter your password, or download the suggested link, attackers gain access to your information or network.
What is Friday Afternoon Fraud?
One of the most common forms of cybercrime in the legal sector, Friday Afternoon Fraud is associated with the large sums of money often transferred at this time of day by house buyers to their conveyancing solicitors’ accounts. Phishing emails purporting to be from the solicitor request the buyer to transfer their personal information or funds into a phony account instead, hoping that the inherent urgency of the transaction means people don’t examine it too closely.
What is a Botnet?
If a robot and a network were to have a baby, but it was an evil baby with multiple heads, it would be a botnet. A botnet is a constellation of web-connected devices infected by a form of malware without the device owners being aware. Using the malware, the attacker can control the group of devices to spread more malware, steal data, or launch a DDoS attack.

What is Email Impersonation?
Email Impersonation is an encompassing term that describes an attacker using your domain, or one which looks very similar, to send phishing emails. It’s not an interchangeable term with Exact Domain Impersonation, where the attacker spoofs your exact domain only.
What are Blacklists and Whitelists?
Imagine the doorman at a party has to decide who to let in and who to turn away. The Blacklist approach is a list of the known havoc-causers and party poopers, so they know who to turn away. The Whitelist approach is to list all confirmed party guests so that only they get in. In email and cybersecurity, the party is the network and the door is the network endpoint. The Blacklist recognizes and blocks all known malware threats, Trojans, scams, etc. The Whitelist allows in only known accepted entities — including software, processes, devices, and email addresses.
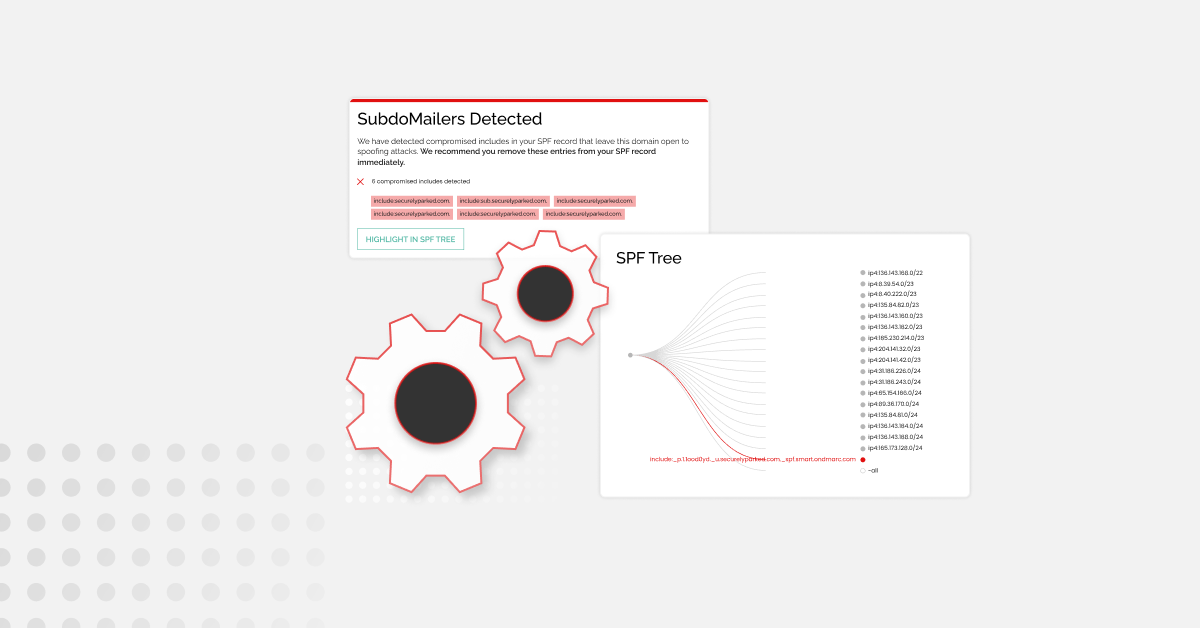
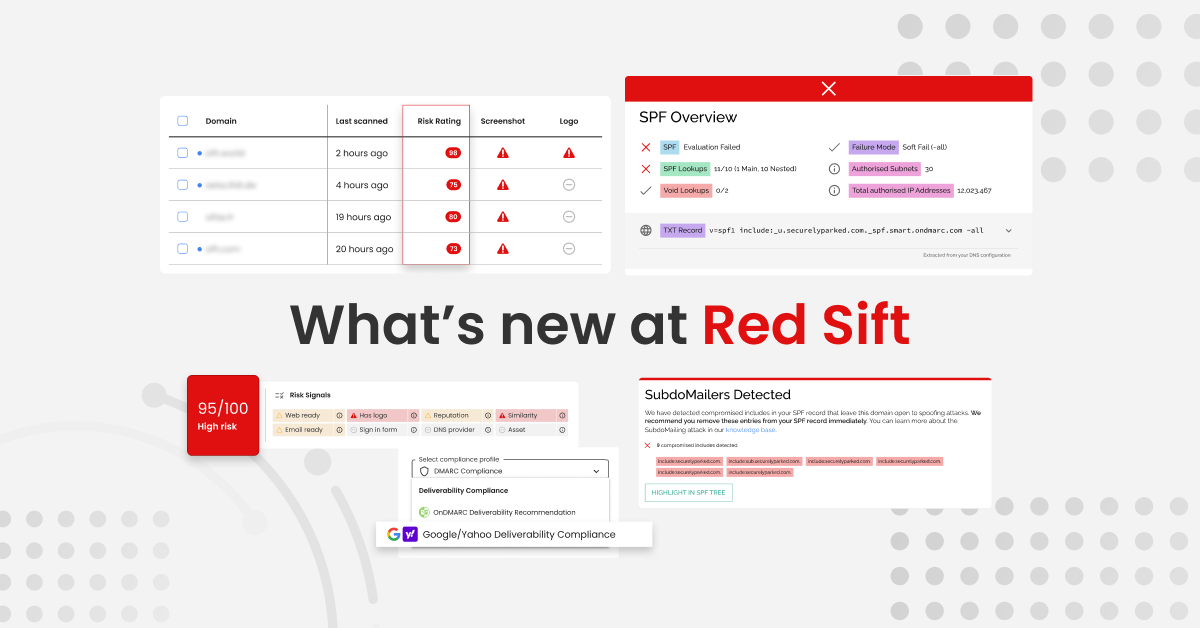
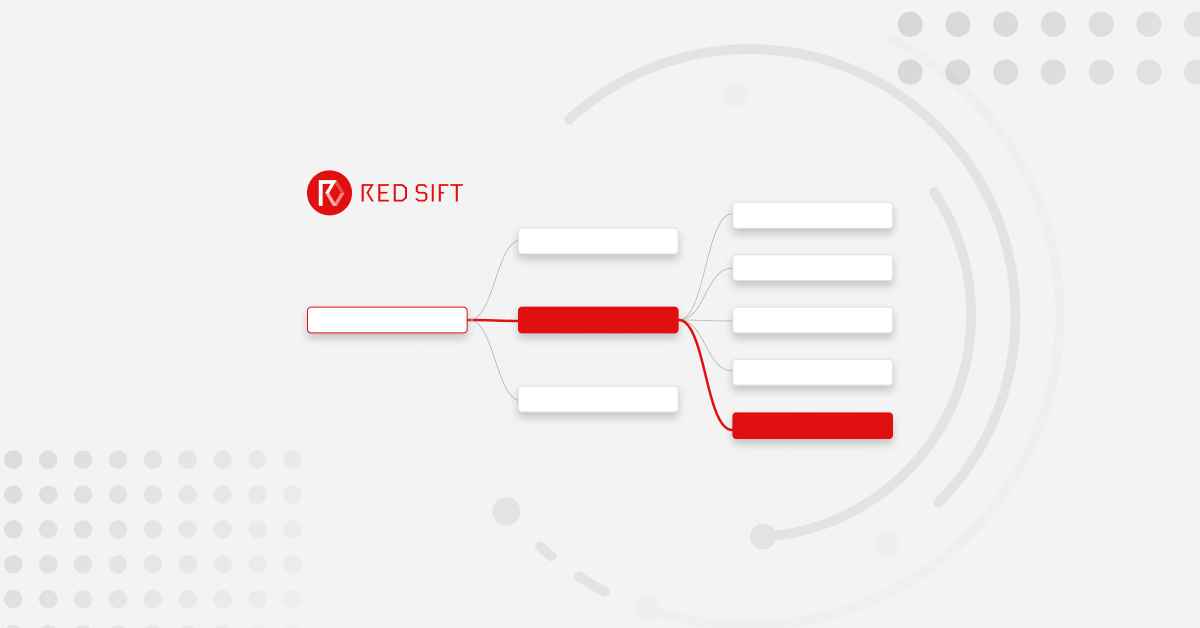
What are SPF and DKIM?
SPF and DKIM are two essential email authentication protocols. SPF stands for Sender Policy Framework, this is essentially a whitelist that outlines the senders that are authorized to send emails on your behalf. Its main goal is to prevent email forgery. DKIM on the other hand stands for Domain Keys Identified Mail, and its primary purpose is to ensure that the email you’re sending hasn’t been modified. Together (and when correctly set up) they create the basis of your email authentication, but to actually stop phishing, you need to also implement DMARC, which works using these.
What is DMARC?
Last but not least, let’s talk about DMARC, Domain-based Message Authentication, Reporting, and Conformance. DMARC is an essential authentication protocol that (when properly configured at a policy of p=reject) protects your domain from exact impersonation and stops hackers from using your domain and brand to send phishing emails. It uses the signals from SPF and DKIM to do this. You can find out more about DMARC works (and its benefits) here.
Check your email security setup today!
So there you have it, all the terms you’ll need to know to get from total newbie to email security boffin! While you’re at it, why not find out what your SPF, DKIM, and DMARC setup looks like with our free investigate tool?