DMARC (Domain-based Message Authentication, Reporting and Conformance) is considered the industry standard for email authentication to prevent phishing attacks. As proud members of Microsoft’s Intelligent Security Association (MISA) we’ve worked to create a unique O365 reporting module for Microsoft customers using OnDMARC. Without this module, crucial DMARC reports would not be available which could mean legitimate emails being blocked when moving to a DMARC policy of full protection (p=reject).

How does this happen?
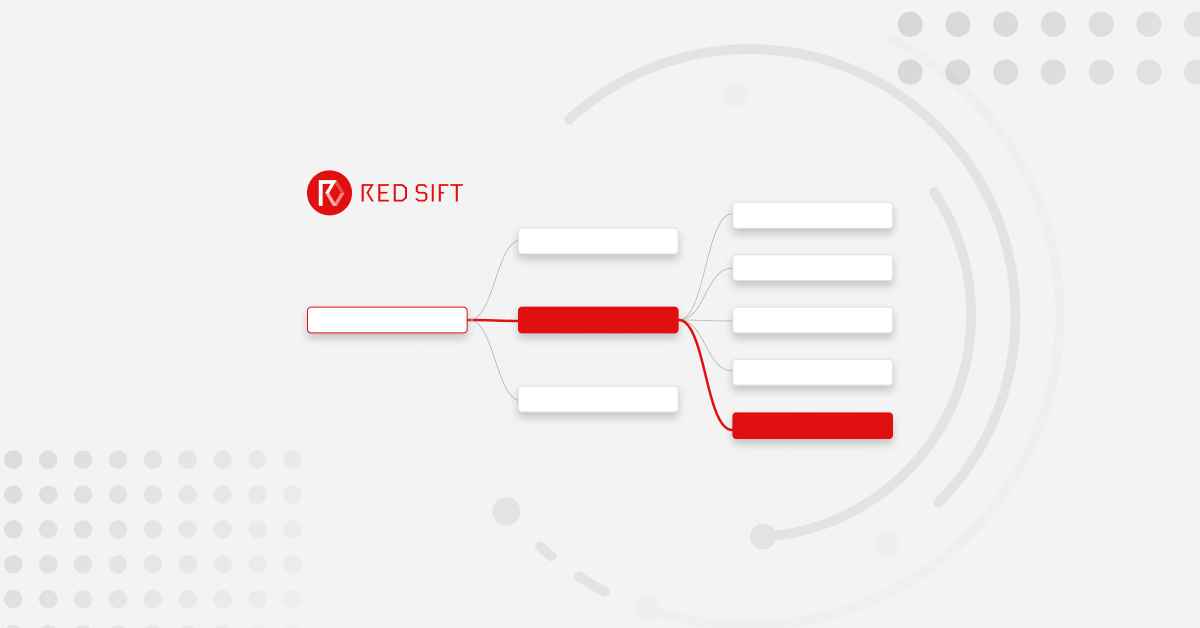
When you invest in a solution like OnDMARC you put a DMARC record in your DNS to be able to view reports sent back from all receiving inboxes. At the moment Microsoft doesn’t currently report on DMARC, which means you could miss crucial insight (and legitimate senders) that could then be blocked from sending emails once you flick the switch to p=reject.
Even if you are already at p=reject, any new services added in the future that report DMARC via O365 may also be missed and blocked without this module.
How will the O365 reporting module resolve this issue?
At Red Sift we pride ourselves on OnDMARC’s full visibility and clear and easy guidance to configure DMARC for your email. This is why we developed a specific solution for the visibility of O365 reports. To sum up, this module adds value if:
• You are working on, or have achieved full DMARC compliance
• You use Microsoft Office 365
• You do not have a third party Secure Email Gateway in front of O365
How does it work?
Office 356 can be configured with our fully supported scripts
to send daily aggregate DMARC reports (in CSV form) to OnDMARC. This data is then surfaced in the Reports section of OnDMARC via a special O365 tab.

One of the things your O365 reporting module will allow you
to do is flag sources seen via O365 that have not already
been seen in your standard DMARC reports. This fixes the blind spot that would have otherwise been there. Without this module you can move to reject and create service disruptions because legitimate O365 senders may be missed.
Attack intelligence along the road to reject
If someone were to launch a highly targeted attack specifically at your employees before you are at policy of p=reject then this too
will not appear in a regular DMARC report and is, therefore, left undetected. Once in reject, these malicious attacks are blocked by OnDMARC, but you would be missing useful intelligence on who attacked your domain without the O365 reporting module. It’s good practice to have full visibility of such targeted attacks as it can be a useful indicator of the threat level the business is experiencing.
How easy is it to set up the O365 module?
We simply provide access to our unique O365 module inside your OnDMARC dashboard which instantly gives you the ability to access the extra reporting functionality for O365. As a fully supported add-on, we will ensure that a member of our support team guides you through the implementation which requires running a few simple PowerShell scripts on your O365 instance.
It is important to note that although Microsoft says they plan to re-enable DMARC reporting in the future they have not yet given a date for this. We fully support our O365 user base and as proud MISA members (Microsoft’s Intelligent Security Association) we have put this crucial module in place to ensure that those invested in DMARC compliance have a straightforward path to reject.
Get in touch today to find out how you can use OnDMARC’s O365 reporting module to uncover blind spots for accurate DMARC compliance.