Investigate is a free tool that instantly verifies if your email security is set up to block email impersonation and what to do if it isn’t!
How does DMARC block email impersonation?
DMARC stands for Domain-based, Messaging, Authentication, Reporting and Conformance. It was ratified so that domain owners could take back control of their email identity, by telling receiving inboxes to reject fake emails impersonating their organization (also known as spoofs). By authenticating an email’s origin with DMARC, email deliverability also improves.
How will Investigate help me with DMARC?
Investigate gives you an easy-to-digest overview of your DMARC setup in seconds, including actionable next steps if something is not configured as it should be.
Two key email security protocols DMARC looks for:
The status of SPF, DKIM, and DMARC is hidden in the email header when you send an email from any of your services. In a matter of seconds and free of charge, Investigate allows you to decrypt these details into meaningful insight and instantly better understand your email setup.
Here’s how Investigate works in 2 simple steps
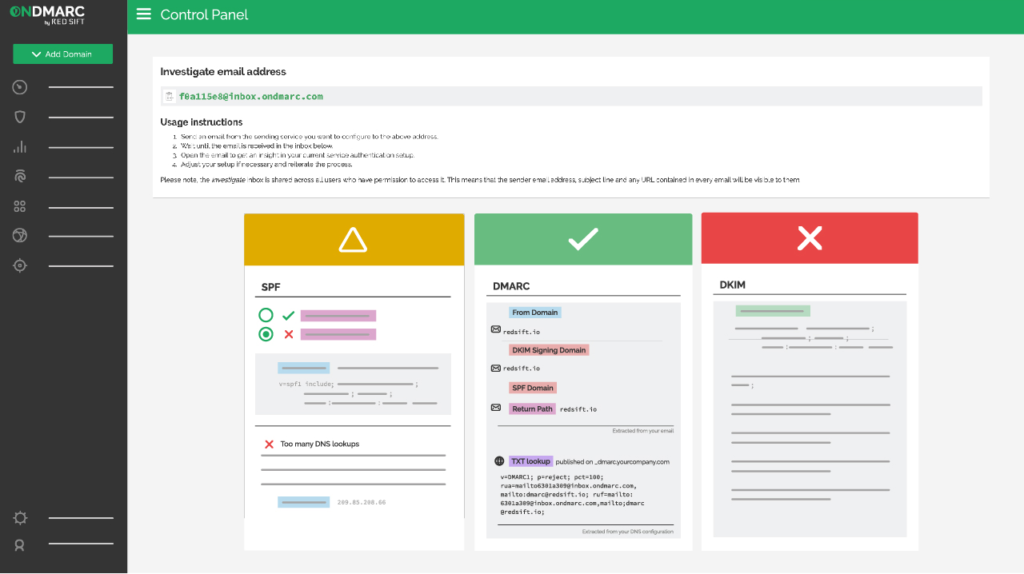
Step 1 – Send an email to Investigate’s inbox
Investigate has a unique inbox that will instantly assess your email security. Simply send an email to its address from the sending service you wish to check.
Step 2 – Get the results!
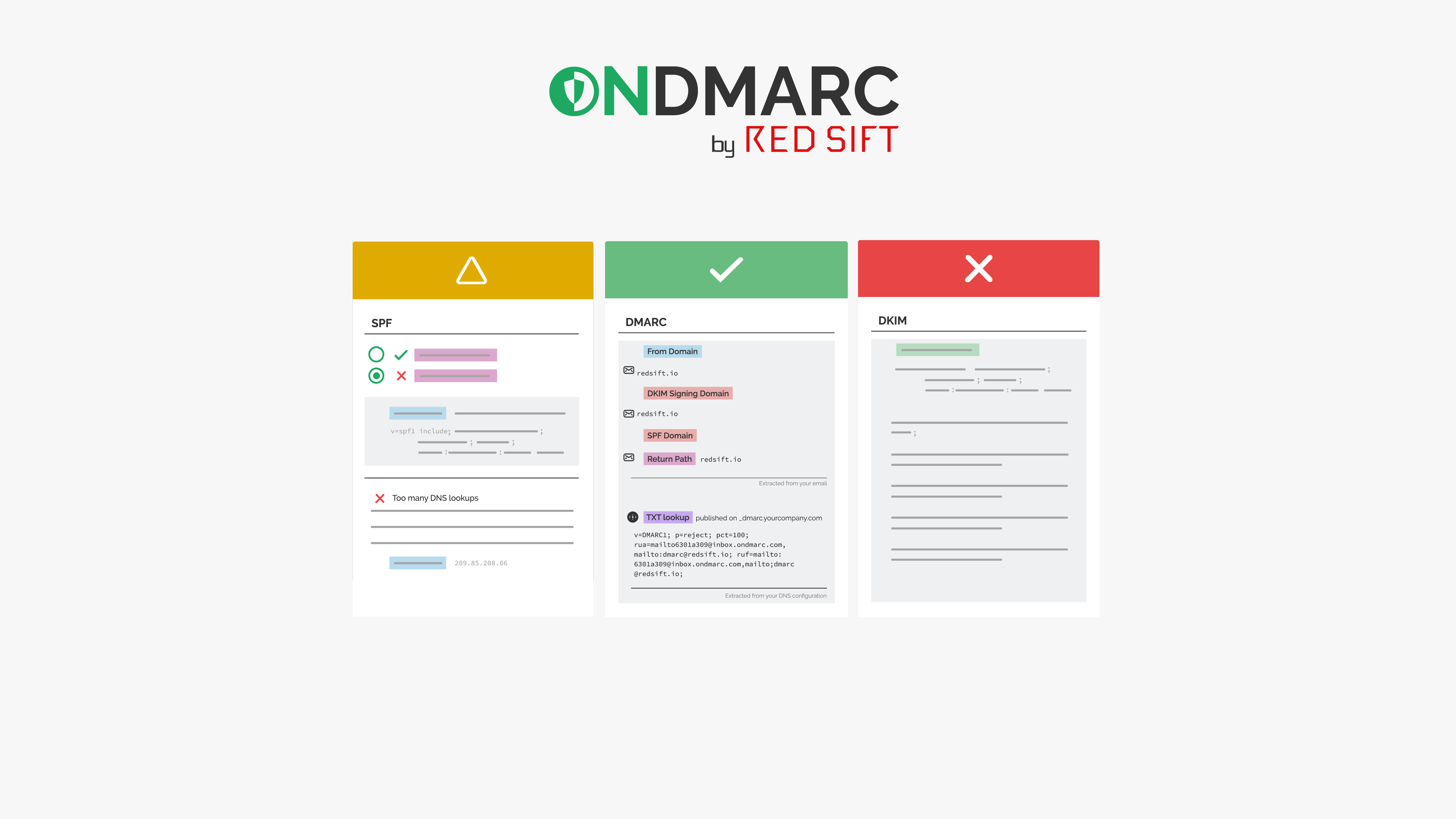
Once your email is sent, your results for DMARC will be revealed with full insight into other areas including SPF, DKIM, TLS and FCrDNS.
The results are clearly presented in a card format, one for each security protocol as shown below:

Each card contains detailed information about the protocol and why it passed or failed. All of the highlighted keywords link to the glossary on our OnDMARC Knowledge Base should you need further information. If you’re struggling to understand your email security setup or looking to take your first steps to improve email deliverability, try investigate today!