If you’re new to our blog, or haven’t encountered email protocols before here’s the top three you need to know:
- SPF: Sender Policy Framework
- DKIM: DomainKeys Identified Mail
- DMARC: Domain-based Message Authentication, Reporting & Conformance
So, why do we care specifically about these acronyms when explaining email security? There’s no mention of spam or gateways, so are they really vital defenses?
2018 saw a 250% year-on-year increase in DMARC policies published, so whatever it is, it’s seeing traction in the market. So let’s explain each acronym and see if we can’t make it simple.
The threat of email-based phishing attacks
Email is a
How many times have you heard about that unwitting victim that paid an invoice because the CEO had emailed for urgent action to be taken to negate late payment fees? And how many times had that email come from a spoofed email account?
So DMARC is a protocol that ensures that emails are authenticated properly and ensures that recipients can rest assured that emails have been sent from legitimate sources, blocking malicious emails from inboxes, and increasing the overall deliverability of authorized emails.
The science bit (Sort of. Actually it’s very straightforward.)
The way that DMARC does this is by using SPF and DKIM, two foundational technologies that help secure different aspects of email and provide a more comprehensive validation.
- SPF verifies whether an email was sent from an authorized IP address.
- DKIM verifies if an email has been signed by the same domain it was sent from or from a domain that is authorized to send on behalf of that domain.
They both produce what is known as authentication identifiers that DMARC uses to authenticate emails and set rules about how receiving servers should treat emails that fail authentication checks.
DMARC is a little bit like a club bouncer who vets visitors – they deny or allow people in based on what the owner has mandated is acceptable; for example dress code, age, and if they’re sober enough to still stand up.
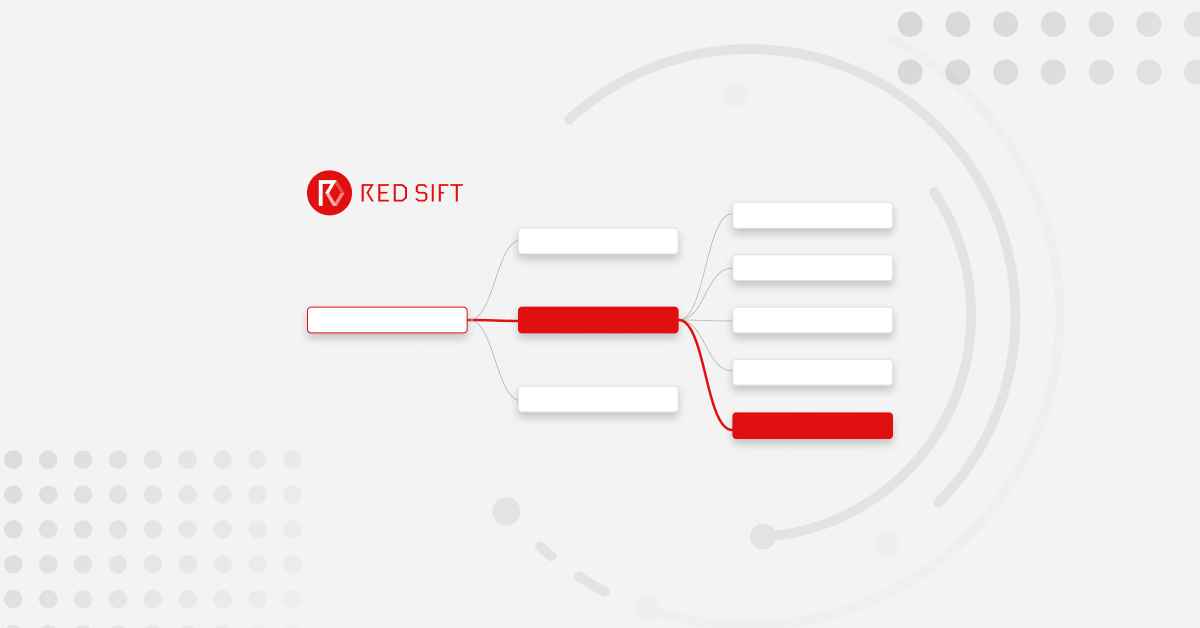
The diagram below shows how SPF, DKIM and DMARC work with each other:

1a & 1b : An authorised and unauthorised message is sent to the receiver’s email server.
2 : The receiver’s server checks the sender’s DNS for DMARC, SPF, and DKIM records.
3 : The receiving server verifies the incoming message against SPF and DKIM and if either validation passes it sends the message onto the recipient.
4: If validation fails, the message will be sent to a spam folder or completely rejected, depending on how DMARC is configured – end user will never see the failed message.
So that’s a basic walkthrough on some regularly used email security acronyms. If this
If you’re unsure whether your organization is using these globally-accepted email protocols, you can use our free investigate tool to check your email setup today.