Here is a situation we have all experienced, the outreach emails have gone out and “Wow! A reply already?!” but upon checking, the response is an automated message informing you that your email was not delivered, or in common English, it has bounced. But, what is a bounce? Why do they occur? And how do they relate to email authentication?
What is an email bounce?
A bounce occurs when the receiving server is unable to deliver the email. There are many reasons which can be easily classified into hard and soft.
- Hard – This indicates that the email has not and will not reach any inbox. There are numerous reasons for a hard bounce, including “Invalid sending address”, the sender being blacklisted, DNS errors, and many more.
- Soft – The email cannot be delivered currently but may be delivered later. Soft bounces are caused by remediable errors such as the mailbox being full or the server being temporarily unavailable.
What happens when an email bounces?
When a bounce occurs, there is an automatic response generated which is then sent to the address listed in the return-path of your email.
The return-path is an address tucked away in the headers of the email, beyond the eyes of the typical user. This address can be the same or a different one from the “From:” address, which is the one immediately visible to the end user.
The return-path address is typically the address of the sender – this is why when an email bounces, you receive a notification to your personal inbox.
In a soft bounce case, the servers will keep trying to send the email. For hard bounces, the email is rejected and the servers will not try to send it again.
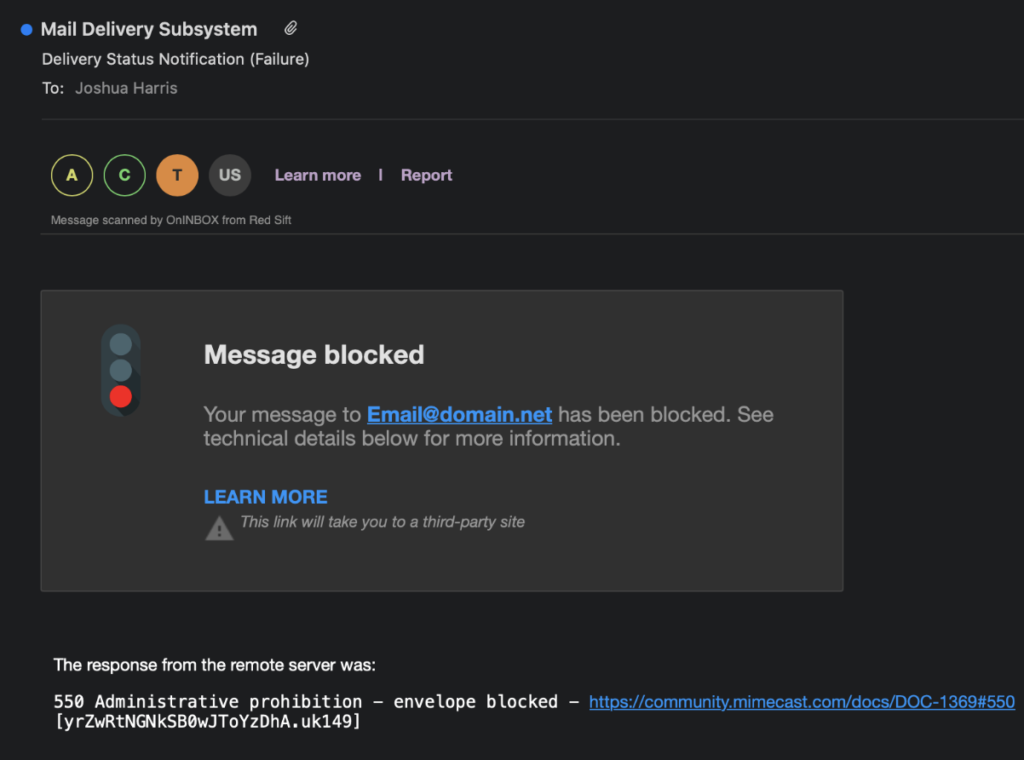
Below is an example of a hard bounce email failure. The error codes will depend on which mail transfer agent sent the bounce back but the full list of errors and reasons can be found in RFC5248.
How does this affect authentication?
To the end user, this all seems relatively straightforward – an email gets sent and if there’s a problem you will be notified. For admins though, management of email bounces ties into authentication and deliverability. It’s important to ensure that bounce rates remain low (ideally under 2% according to independent research by Campaign Monitor). It is also important that your email authentication is robust and enforced by DMARC so that the domain is protected against spoofing.
Authentication of an email’s IP address is done using the SPF protocol, this checks that the sender IP is listed in a record at the domain referred to in the return-path.
Deliverability is also a key factor to consider here. Mail servers may classify a sender as spam if that sender sends too many emails that get bounced, as it shows poor management of the sending list. As a result, many sending services will modify the return-path to point to the sending service’s address, helping them to capture the bounces which subsequently are presented to the user to help them better manage the sending list.
A side effect is that the SPF check is performed on the domain of the sending service, which breaks the SPF alignment component of the DMARC protocol (e.g sending service = “example.com” and return-path = “company.com”) and makes DMARC authentication based on SPF not possible.
DMARC not only checks for alignment in the SPF protocol between the return-path and the “From:” address, but also checks for alignment in the DKIM protocol between the domain in the “d=” parameter and the domain in the “From:” address.
If the return-path points to the sending service’s domain rather than the “From:” address, then the DMARC check will rely entirely on the DKIM protocol to pass authentication.
Deliverability and authentication, separately, have protocols and mechanisms in place to handle these processes but the handling can clash when DMARC gets involved due to alignment.
The solution to this is to ensure that any sending services you use support DKIM and also that supports authentication of your custom domain, this concept is called whitelabelling. Without this, you won’t be able to provide authentication for those emails and also you won’t be able to reach protection mode in your DMARC policy for the domain on behalf of which this service sends emails.
To explore the setup of your email authentication, send a test email to our free ‘Investigate’ tool below.