In October 1971, computer engineer Ray Tomlinson successfully managed to get an email message to send from one computer to another sat beside it via ARPANET, a network of computers that served as a precursor to the internet.
While email turned 50 years old in November 2021, it wasn’t until the commercialization of the internet in the mid-90s that it truly took off as one of the world’s preeminent communications tools. Unfortunately, its rise also spawned meteoric misuse as unscrupulous scammers began peddling unwanted products, bogus deals, and even computer viruses to the masses.
The phishing scam is more than 20 years old
Yes, email scams are over two decades old. In fact, phishing scams , long associated with email, actually began a few years earlier via AOL instant messaging, with attackers posing as AOL staff and demanding that users verify their accounts by handing over passwords or billing information.
However, as email took over as the preferred means of customer and organization engagement, scammers quickly switched over to exploit this channel. E-gold, a digital gold currency founded in 1996, was one such target for phishing exploits and financial malware while email scams were in their infancy.
Attacks against the company culminated in a major phishing scam in June 2001, targeting members of its mailing list. This was then followed post-9/11 by a second round of phishing, disguised as ‘identity checks’.
Financial institutions are a scammer’s delight
Financial institutions were always an obvious target for scammers. These organizations not only hold rich datasets on their customers but if scammers can get hold of customer account details too, they can easily steal from them directly. No surprise then that the technique used in the e-gold phishing scam was quickly adopted for use against customers of other financial institutions as well.
eBay and PayPal were two more companies that found themselves on the wrong side of email scams a decade ago, and they’re still battling to rid themselves of email impersonation today. Back in 2006, it was revealed that 75% of all phishing scams were focused on eBay and Paypal, with phishing emails taking recipients to imitation websites and using their login details to commit identity fraud.
Another popular victim of the email scam was HMRC. Not only was it a ‘trusted’ entity in the eyes of email recipients, but it could legitimately demand specific pieces of personal or financial information from recipients. It took HMRC until 2007 to publish its first piece of guidance regarding phishing emails and bogus communications. This came in response to a spate of fraudulent emails advising recipients that, ‘After the last annual calculations of your fiscal activity we have determined that you are eligible to receive a tax refund of £210. Please submit the tax refund request and allow us 6–9 days in order to process it.’
The tactic adopted by these scammers was markedly different to some of those gone before; instead of scaremongering, the authors attempted to induce recipients into parting with their details based on the promise of a financial rebate. It was a highly successful change of approach that led to a major upsurge in HMRC-related scams, to the extent that by 2016, a Which? survey found that 40% of adults had received phishing emails purporting to be from HMRC.
Make way for DMARC authentication
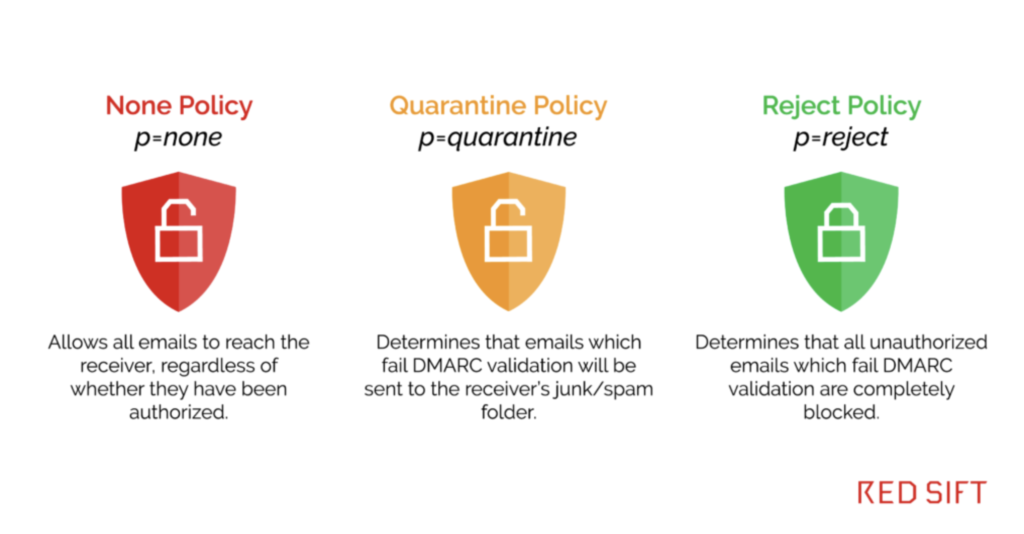
In response to this, HMRC deployed email authentication protocol DMARC (Domain-based Message Authentication, Reporting, and Conformance). DMARC is globally acknowledged as the only way to guarantee the legitimacy of email ‘from’ addresses, and drive down spoofing attacks. In 2016 HMRC was able to stop 300 million phishing emails using their domain simply by achieving DMARC protection at p=reject.
DMARC is essential for all businesses in 2022
So where does this leave us now? Well, email security providers continue to try and block fraudulent messages from false domains that purport to be from some of our well-recognized companies. They also attempt to identify more personalized, targeted attacks that seek out known customers of other, perhaps less prominent, organizations.
But where these systems fail is in clamping down on email impersonation from legitimate email domains. The www.gov.uk domain may now be safe from spoofing attacks thanks to DMARC deployment, but the same cannot be said for many other private sector domains.
It’s 50 years since the first email, and more than 20 years from the first email scam, yet this blind spot in organizational email security defenses remains worryingly exposed. To find out more about DMARC, how it can help protect your business and wider network from phishing scams, and what to look for in a DMARC solution, download our free Buyer’s Guide today.