In this second instalment of “The Data Must Flow” we are doing a deep dive on data flows, which the Biden Administration notes are critical to enabling the $7.1 trillion EU-U.S. economic relationship and which the World Economic Forum regards as an essential pillar of the global economy. We are also taking a serious look at new privacy regulations, data frameworks, and the return on investment for cybersecurity compliance.
In the latest Ask the Expert, hosts Rois Ni Thuama and Sean catch up with Linda V. Priebe, JD, CIPP/E. Linda is a partner in the Washington DC Office of Culhane Meadows PLLC where she focuses on EU and U.S. Data Privacy/Protection/Security Compliance and Co-Chairs the Government, Regulatory, and Compliance Practice Group. Serving fourteen years in various capacities in White House offices, Ms. Priebe has also been a trusted legal advisor to three U.S. presidential administrations.
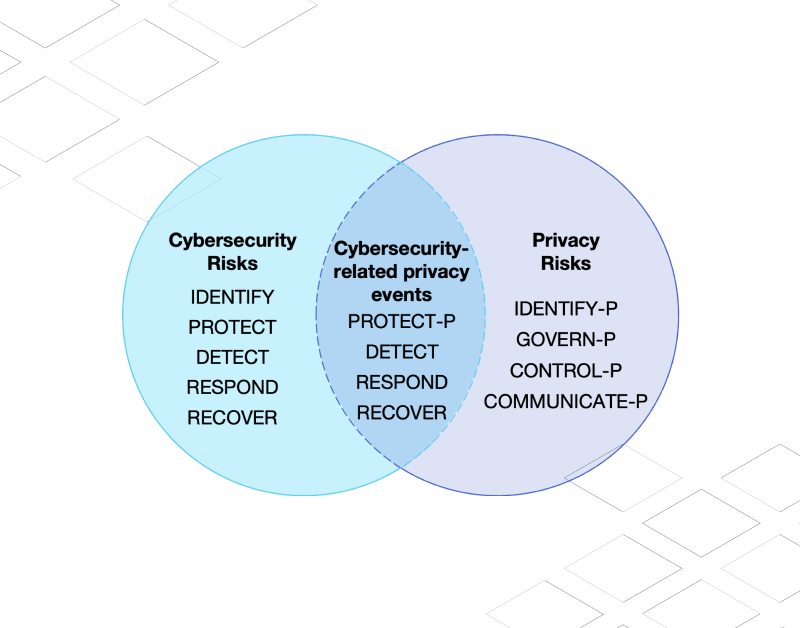
The C-Suite and Boards have significant responsibility for privacy, security, and data flows. Boards have more than simply a fiduciary responsibility to oversee C-Suite performance or show that cyber risk is being reduced through investments. Today, boards also need to understand their organization’s exposure to risk, whether the organization is meeting regulatory requirements and complying with data protection laws, and what resilience measures are in place or should be implemented.
Boards and the C-Suite are also going to be keen to understand the ROI for cybersecurity compliance around data, which can be especially difficult to quantify. After all, such analysis likely involves largely intangible factors such as reputation or customer trust. However, by implementing effective cybersecurity measures and proactively meeting data compliance requirements, businesses can reduce the risk of costly data breaches, minimize downtime, and potentially reduce insurance premiums, among other benefits.
Some key takeaways from our discussion with Ms. Priebe include:
- Compliance and transparency are attracting the attention of prospective global business partners.
- For businesses, the costs of non-compliance with data privacy regulations are rising. For example, the Illinois Biometric Privacy Act provides redress for every incident of collection, even in the employee context.
- While the US does not yet have a national, federal, comprehensive data privacy law, pressure is mounting for one.
- The United States Department of Justice has taken notice that top leadership of companies have opportunities to respond to cybersecurity and that personal accountability is now on the table for failings.
- Businesses that treat cybersecurity compliance as an opportunity to get ahead tend to thrive and avoid poor outcomes.
- Good cybersecurity and compliance attracts business, partnerships, and helps retain talent.
- Aligning business objectives with security concerns is about more than simply averting disaster.
- There is value in proactively adapting your business to the strictest standards.
- Dollars invested in compliance return a significant investment.
And that last point is critical. A positive ROI for cybersecurity can provide a strong justification for ongoing investment to protect your organization from cyber threats and build resilience.
So if you are in the C-Suite and thinking about cybersecurity compliance, would you be happy with a return on investment for cybersecurity of 2 to 1? Or are you content treating the cyber ROI as more art than science? In our discussion with Ms. Priebe, we learned that the ROI for complying with data privacy and cybersecurity regulations could be as high as 7 to 1. While that might be an outlier, there’s a clear need to understand more in this space, particularly as we consider the challenges of cyber insurance and the critical need for enterprise scale resilience.
To learn more, listen to the interview or read (and share) the transcript here. Next in Ask the Expert, we will be talking geopolitical risk, cybersecurity, and insurance with Harpreet Mann, President of Amynta Trade Credit and Political Risk Solutions.