By Dr. Sean Costigan, Director of Cyber Policy for Red Sift
As our digital world grows increasingly interconnected and attack tactics and techniques grow both prevalent and more sophisticated, cyber resilience is a requirement for modern organizations. Yet achieving resilience remains elusive for most.
To help organizations achieve cyber resilience, Red Sift conducted a global survey of top executives across diverse industries to better understand the challenges and opportunities they face in safeguarding their digital assets. We released the survey findings today in a new in-depth report, the “State of Cyber Resilience 2023.” Results in the research report underscore the critical role that visibility, information sharing, risk management, emerging frameworks, and regulations play in ensuring organizations remain adaptive and resilient amid today’s rapidly evolving threat landscape.
Key takeaways from the Red Sift cyber resilience research report include:
Evolving threat landscape
While many large corporations have invested significantly in cybersecurity, small and medium-sized enterprises (SMEs) often need more resources and capacity to onboard expertise to meet changing requirements for cybersecurity, not to mention defend against advanced threats. Findings in the report show that organizations of all sizes are skipping cybersecurity basics. For example, the results from our research suggest that over 40% of the organizations surveyed have yet to prepare written plans to communicate when an incident has occurred.
Pursuing organizational readiness
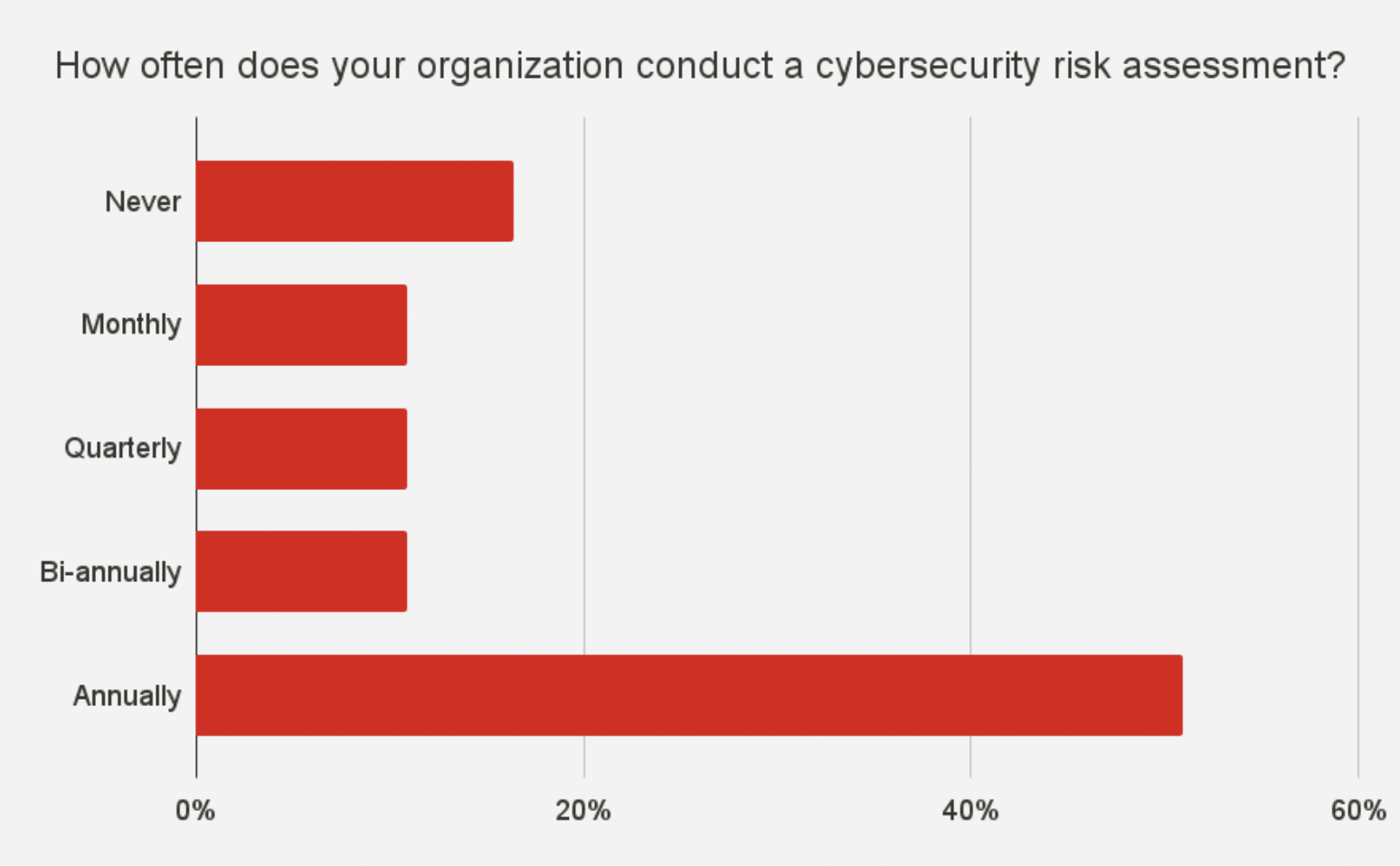
Many organizations fall short on consistent, scheduled assessments of cyber risks and vulnerabilities. Periodic audits enable companies to identify and remediate gaps before incidents strike. However, the survey indicates risk assessments are still infrequent for a large portion of firms. More directly, most organizations, regardless of size, are skipping cybersecurity basics. The survey results indicate that a significant number of organizations still need to conduct periodic or consistent risk assessments, leaving them vulnerable to surprise.
Changing regulatory environment
Governments are becoming more proactive in issuing guidance and legislating cyber policies. The global cybersecurity landscape is witnessing considerable transformation through regulatory changes. These regulatory changes force organizations to prioritize data protection, privacy, and risk management. At present, this is having mixed results. In some cases, regulations may be misaligned between countries, creating challenges for multinational corporations even within regulatory blocs like the European Union (EU). The goal, however, is to improve confidence in markets and critical infrastructure by building cyber resilience into the fabric of organizations.
Expanding frameworks
Cybersecurity guidance and frameworks are undergoing dynamic changes to adapt to the evolving threat landscape and the increasing complexity of digital ecosystems. Governments and framework-developing bodies worldwide recognize the importance of a secure digital environment and are taking proactive steps to expand existing frameworks to enhance cyber resilience. As technology advances and organizations become more interconnected, widely adopted frameworks augment their scope to encompass a range of risks and challenges.
Our research finds notable shifts in the integration of risk-based approaches, emphasizing the need to prioritize security measures based on the potential impact of threats, the need for transparency for stakeholders, and expanding the understanding of cyber as an enterprise-wide risk. As we detail in this report, the U.S., Europe, and industry groups have made significant strides in new frameworks for resilience.
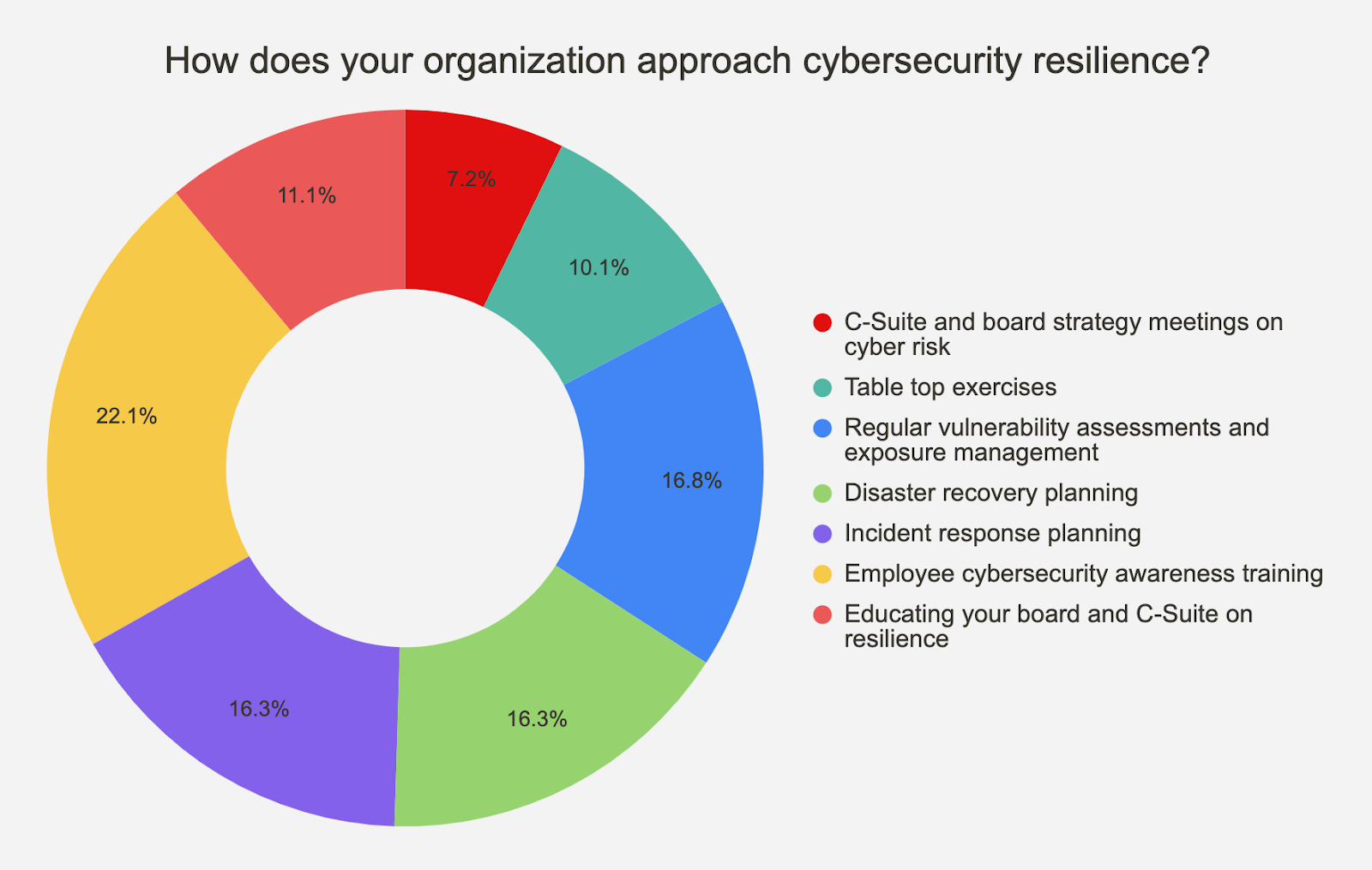
Understanding the criticality of people in cybersecurity
Human factors play a pivotal role in cybersecurity, underscoring the critical interplay between technology and human behavior. Despite technological advancements, humans are both the weakest link and essential component in the security chain. Understanding cognitive biases, promoting critical cybersecurity awareness, and providing judgment-free training is key to mitigating human-related vulnerabilities. As cybersecurity threats evolve, recognizing and addressing the human element is essential for building resilient defense mechanisms that account for the complexities of human behavior within the digital landscape. The global shortage of cybersecurity professionals continues to be greater than three million people worldwide. More challenging still, organizations that suffer serious cybersecurity breaches often see significant numbers of hard-to-replace staff depart.
Considering the complexity and pace of change in modern technological environments and the scale of cybercrime, cyber resilience presents a moving target.
To quote Red Sift CEO, Rahul Powar, “Proactive cybersecurity is the shield that guards your digital fortress before an adversary strikes. Resilience is what turns setbacks into stepping stones.”
Organizations can begin turning aspiration into action by increasing visibility into their attack surface and prioritizing the protection of their crown jewels while following research-backed recommendations, aligning with frameworks, and complying with regulations.
You can download the full State of Cyber Resilience 2023 report here.