“In the midst of every crisis, lies great opportunity”. Inspiring as it may sound, Einstein was probably also sending us a warning, a warning about the opportunists in our midst. Regardless of the nature of the crisis, there’s always a group of people that will look to capitalize on the misfortunes of others. Whether that be hoarding essential items during wartime rationing and selling on at an eye-watering markup, or preying on vulnerable people during a global pandemic, again, all in the name of making a quick buck.
Nobody in the cybersec industry has been surprised at the number of cyberattacks witnessed over the past month in response to Covid-19. At a time when uncertainty and instability are high, and reasoning is mired with panic, it’s the perfect time for scammers to try and trick individuals and organizations into handing over sensitive information and money.
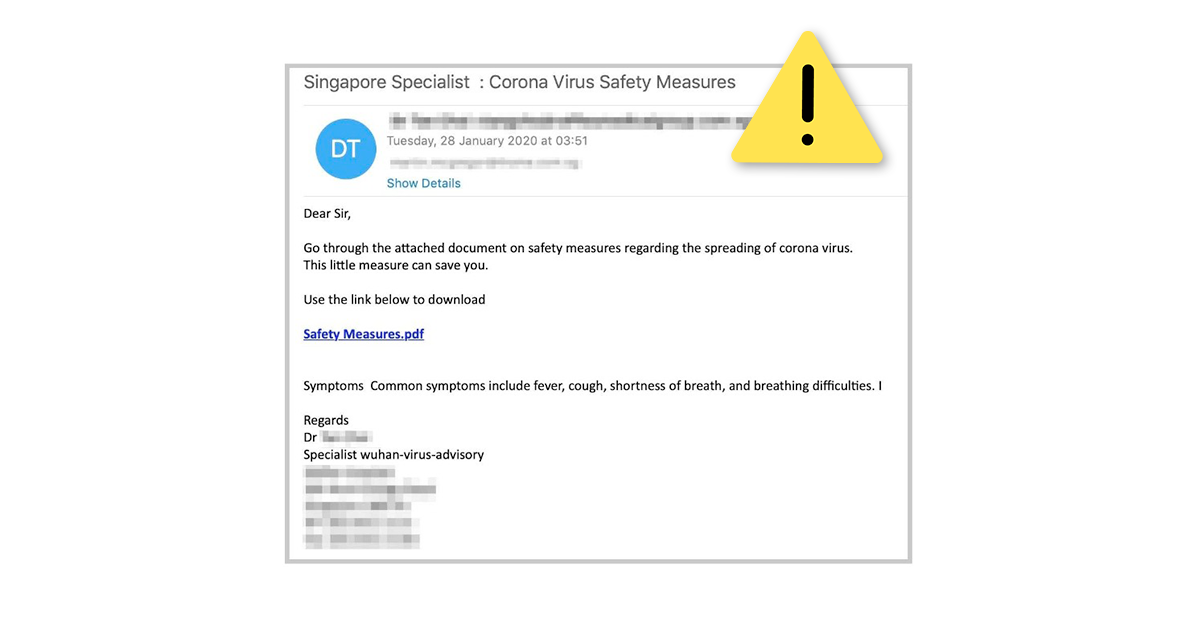
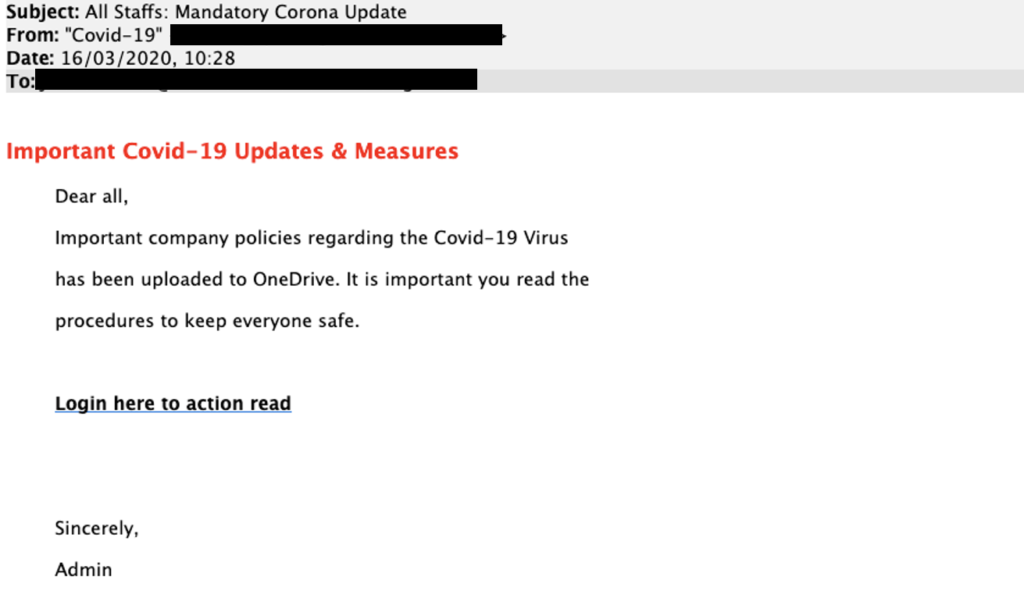
Examples of Covid-19 scams
Earlier this week, MediaPost reported on a large-scale phishing attack targeting the majority of office workers now working from home. These ‘credential-stealing’ scams pose as your employer, either an exec or HR representative, and advise you to follow advice via a document available on OneDrive. You’re asked to login via a link in the email, and of course, your data is then harvested by the criminals and your corporate credentials, are compromised.
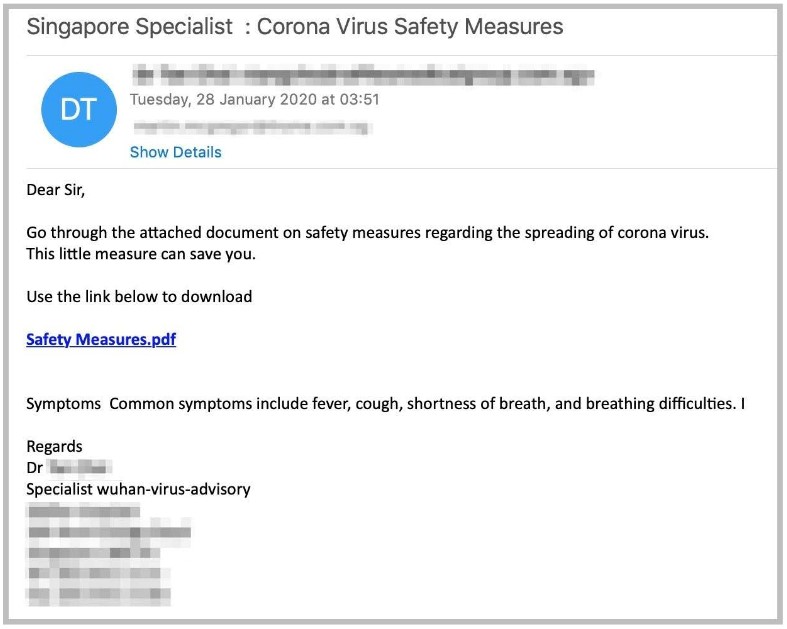
There have also been multiple reports of phishing emails purporting to come from the Center for Disease Control and the World Health Organization. In a time of crisis, the public will look to their national authorities or global bodies for advice and information on the subject matter so it’s a no-brainer scam to undertake. In these instances, recipients of these faked emails were asked to use their email login to obtain vital information about the virus and keeping safe.
Taking precautions
Jumping on the bandwagon of a major global news event is not a new tactic for cybercriminals, and many people now know what checks to make to see if an email is legitimate. But this Covid-19 crisis is going to be high on the news agenda for months to come and impacts every single person, so scammers have a much wider and more vulnerable range of targets than ever before.
Whether you’re a business or an individual navigating the internet at this unprecedented time of increased digital usage at home, the potential for human error will no doubt increase, so here are some tips to help you stay safe and avoid these unscrupulous emails.
Organizations
Protect your employees from being caught out by fake emails from the company. Deploy email protocols that will eradicate the possibility of scammers impersonating your domain. This will also safeguard your customers – if criminals can’t spoof your email addresses, customers can rely on key identifiers to weed out the legitimate from the illegitimate.
Individuals
Check the sender’s domain against the actual website domain of the organization in question. For example, ‘@cdc-gov.org’ versus ‘@cdc.gov’ – which one is correct? There are a host of spelling and grammar checks you can make, along with tone – do you feel rushed? Pressure to ‘act fast’ is a common tactic of scammers wanting to rush you into handing over information.
Try out our free ‘Investigate’ tool below to check the status of your DMARC configuration and keep protecting your workforce wherever they may be working.