In days gone by, when an organisation wanted to protect its cyber defences, the norm would be to bring in a cyber consultant or agency. Whether it was a someone-who-knew-someone-who-knew-someone kind of contact or an established name like Capita, they would act as the go-to source of cybersecurity knowledge and execute a strategy to protect the company’s cyber defences. In the early days of cybersecurity, this largely made sense: the knowledge was held by a select few, who because of their expertise could charge huge sums of money for their time and contribution.
In the past few years however, that trend has been increasingly shifting. Once, protecting your company’s cyber presence was a 90% human affair, with 10% technology thrown in for good measure – mostly for the consultants to keep notes and records on their computers. Today, the balance has completely shifted. Numerous tasks once reserved for the pedestalled consultant, from data input to processing to trends analysis and reporting, are increasingly filled by software, programmes and platforms.
For better or worse
Ok, but in an increasingly digitised world – where you can play pro-level chess against an automated bot, do your weekly shop at Amazon Go without speaking to a single soul, or have your voice assistant control the security of your home, car and hamster – is reigning back the human element to cyber consultancy for the best, or is it just following the trend?
The thing about employing computers rather than consultants is not about digitising for the sake of it, it’s about using technology to execute the easy, mundane, repetitive tasks that would otherwise take huge amounts of human resources. Why have a member of staff manually comb through thousands of data sets to look for an anomaly, like a vulnerability in your email domain, when you could use a computer programme to execute the same task in a fraction of the time, and with a sliver of the resources?
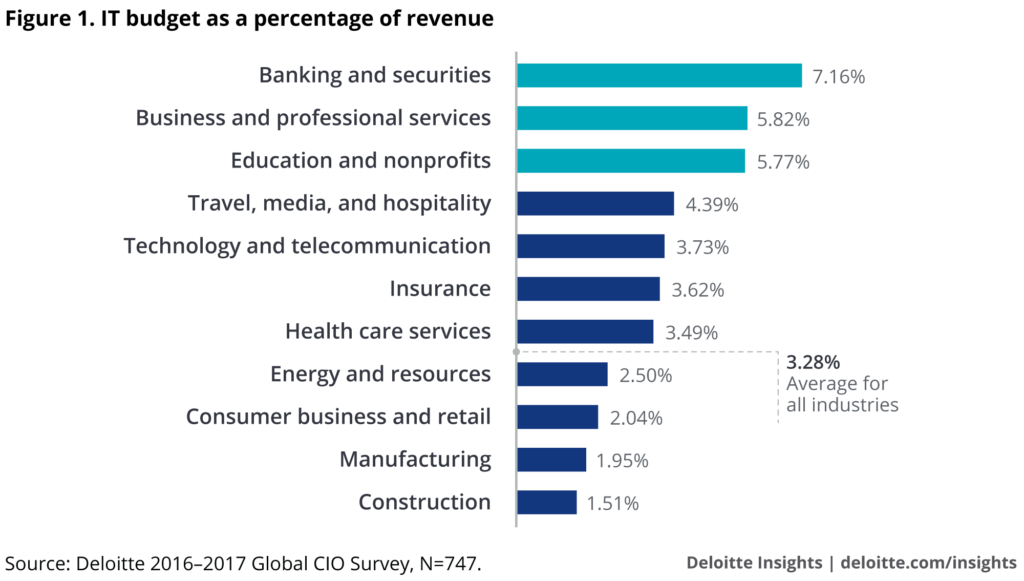
When stuck between a rock and a hard place, faced with either prohibitive consultancy costs or weak cyber defences, AI-powered cybersecurity offers a more accessible means of gaining the knowledge and tools required for effective cyber protection. Considering that average business is spending around 3% of their revenue on IT, the need for cost-efficient IT solutions is even more pressing for companies with limited budget and resources like startups and SMEs.
AI-powered cyber solutions allow companies, organisations and individuals to take back ownership of their cybersecurity. AI can be used to automate the complex aspects of implementing and maintaining protections, while processing the data to make key findings and actions more accessible and digestible to the untrained eye, and negating the need to bring the costly consultant down from their ivory tower.
A new age consultant
It’s about using technology to enhance people’s ability to do their jobs, using techniques like automation, machine-learning and natural language processing, so that your employees can focus on the areas where people can add real value for the company and its customers. Talking a customer through a new feature their product offers, for example, or onboarding a new team in the customer’s company; instances where a human approach provides the best quality service.
When you look at it this way, it makes complete sense. With cybersecurity, it’s about what AI and machine learning can process and make accessible to users, rather than having to shell out for expensive consultants to help fight cybercrime, while remaining in the dark about what that really means.
Not only does pivoting towards tech-based cyber solutions reduce the pressure on your teams, but it’s a more affordable and more scalable means of protecting your organisation’s cybersecurity.
This isn’t to say that consultants no longer have a role in the world of cybersecurity; they can and do provide organisations with valuable advice and support in navigating an increasingly complex world of enterprise security. And there will always be a need for this. But the role of the consultant should no longer be based on keeping information and insight from people, to be shared only with those with the deepest pockets. Instead, it needs to be about how consultants can make necessary information more accessible to the people who need to understand it. Using AI-powered cyber solutions not only frees up the consultants’ time and resources to be applied to the highest value, most complex work, it also democratises access to cybersecurity by fundamentally lowering the starting price point and simplifying the user experience.